Shadow Admin Discovery and Remediation
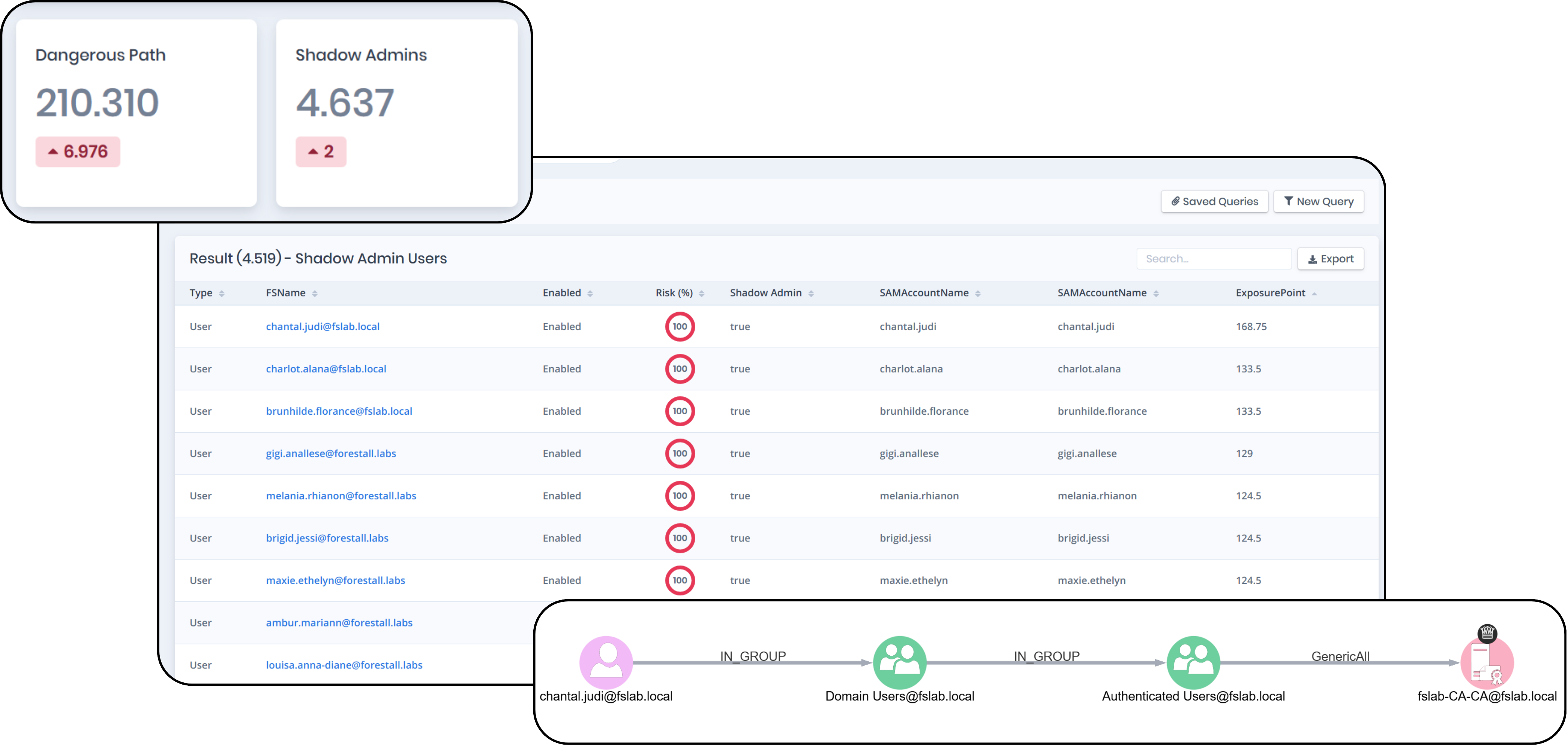
Scenario: Security leadership suspects that many identities have indirect administrative access through delegation chains and group nesting, but cannot quantify the scope.
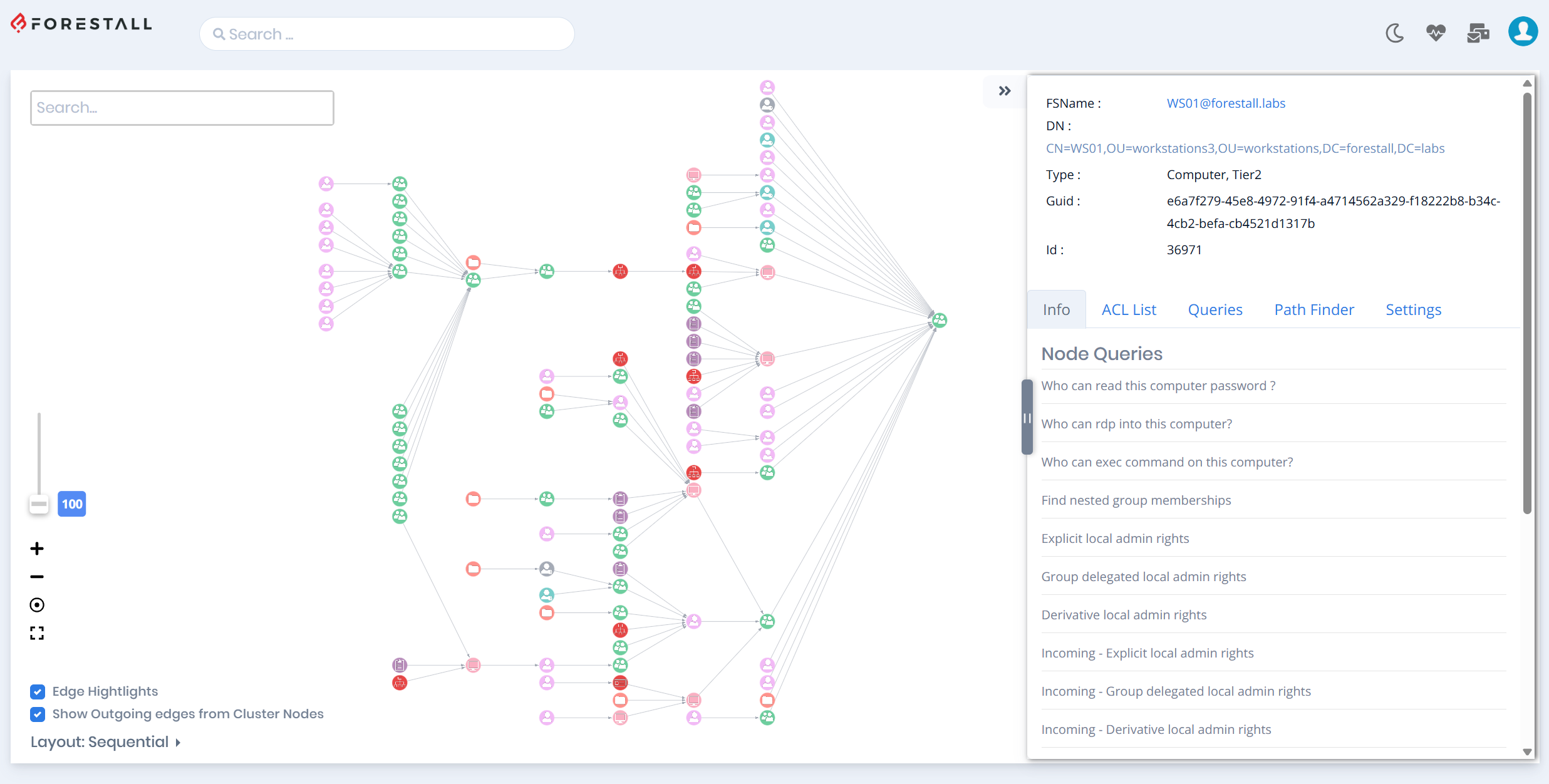
How Forestall helps:
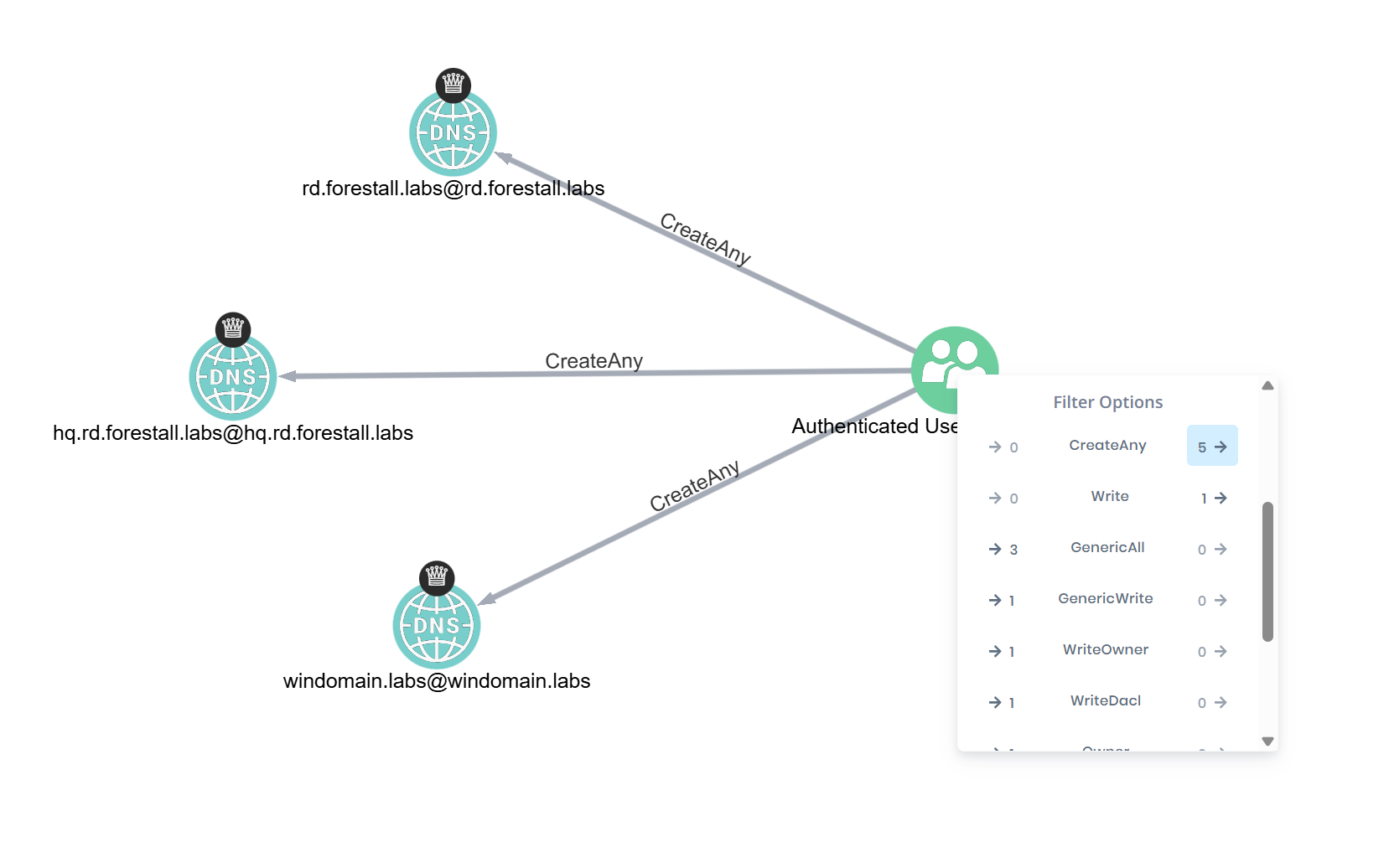
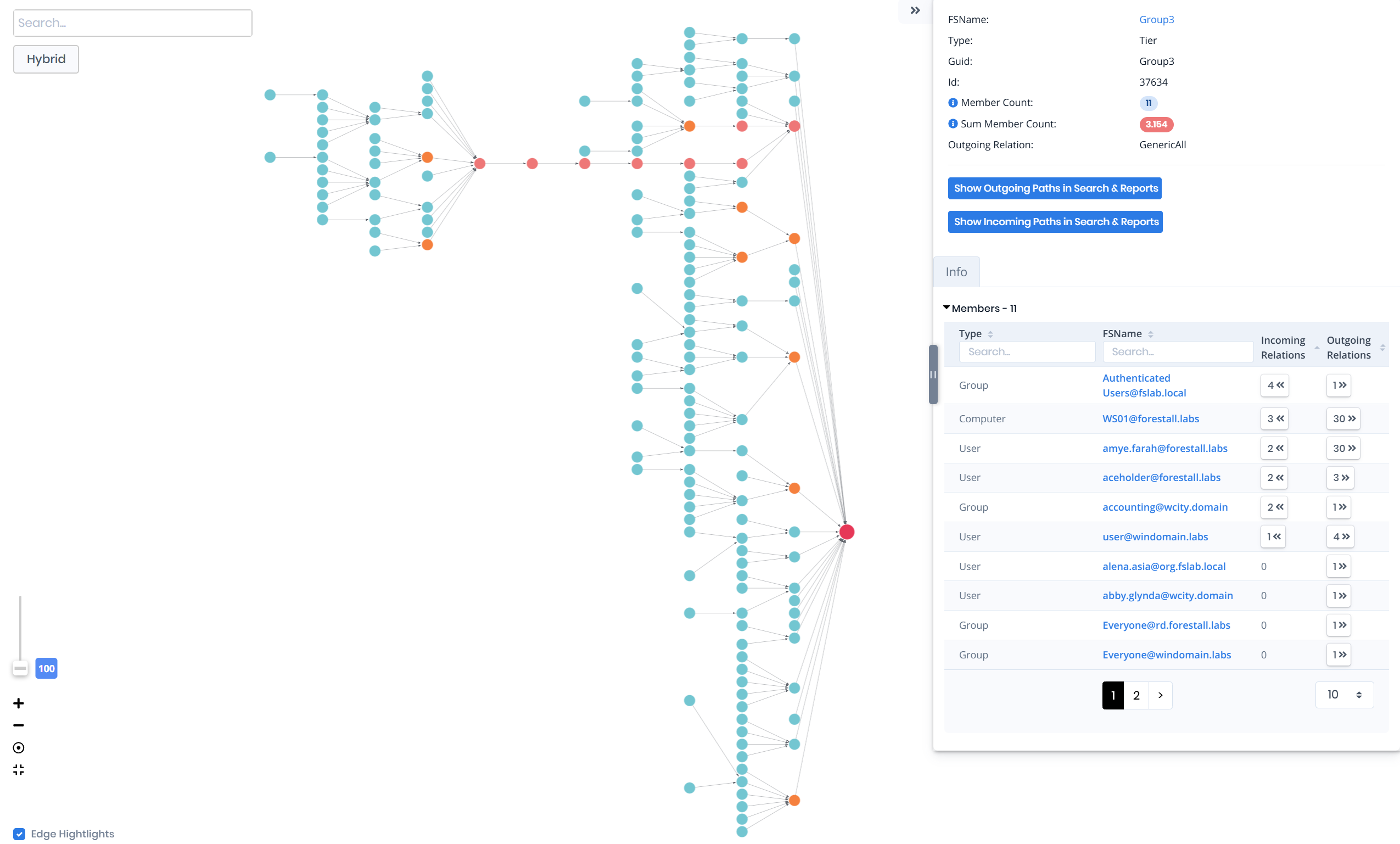
- Automatically label all Shadow Admins with paths to Tier 0
- Quantify the total number of indirect administrative paths
- Identify chokepoint objects whose remediation eliminates the most Shadow Admin paths
- Track Shadow Admin count reduction over successive remediation cycles