M&A Identity Due Diligence
Scenario: During a merger or acquisition, the security team needs to understand the identity posture of the target environment before integration begins.
How Forestall helps:
- Deploy read-only connectors to the target environment without requiring admin access
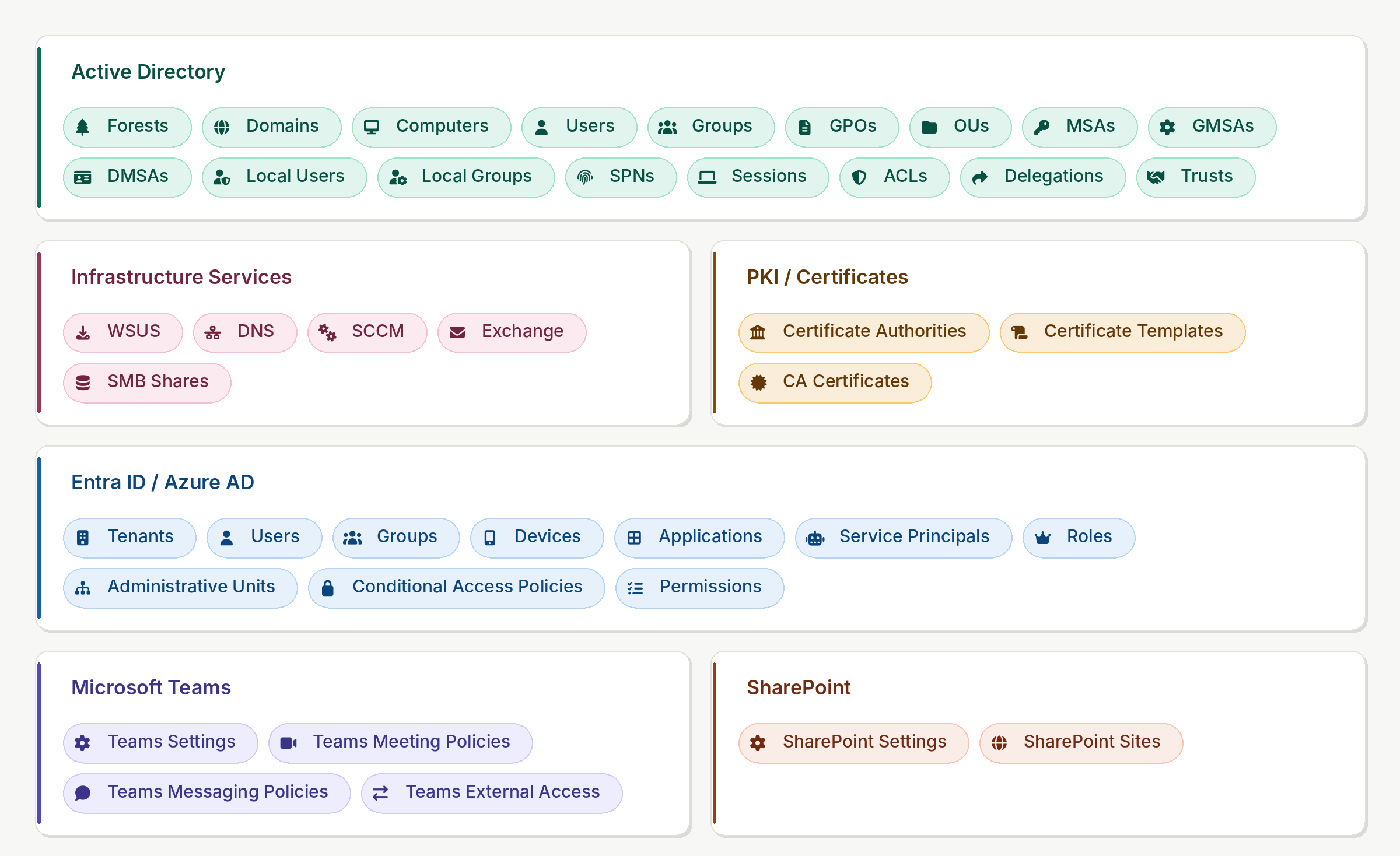
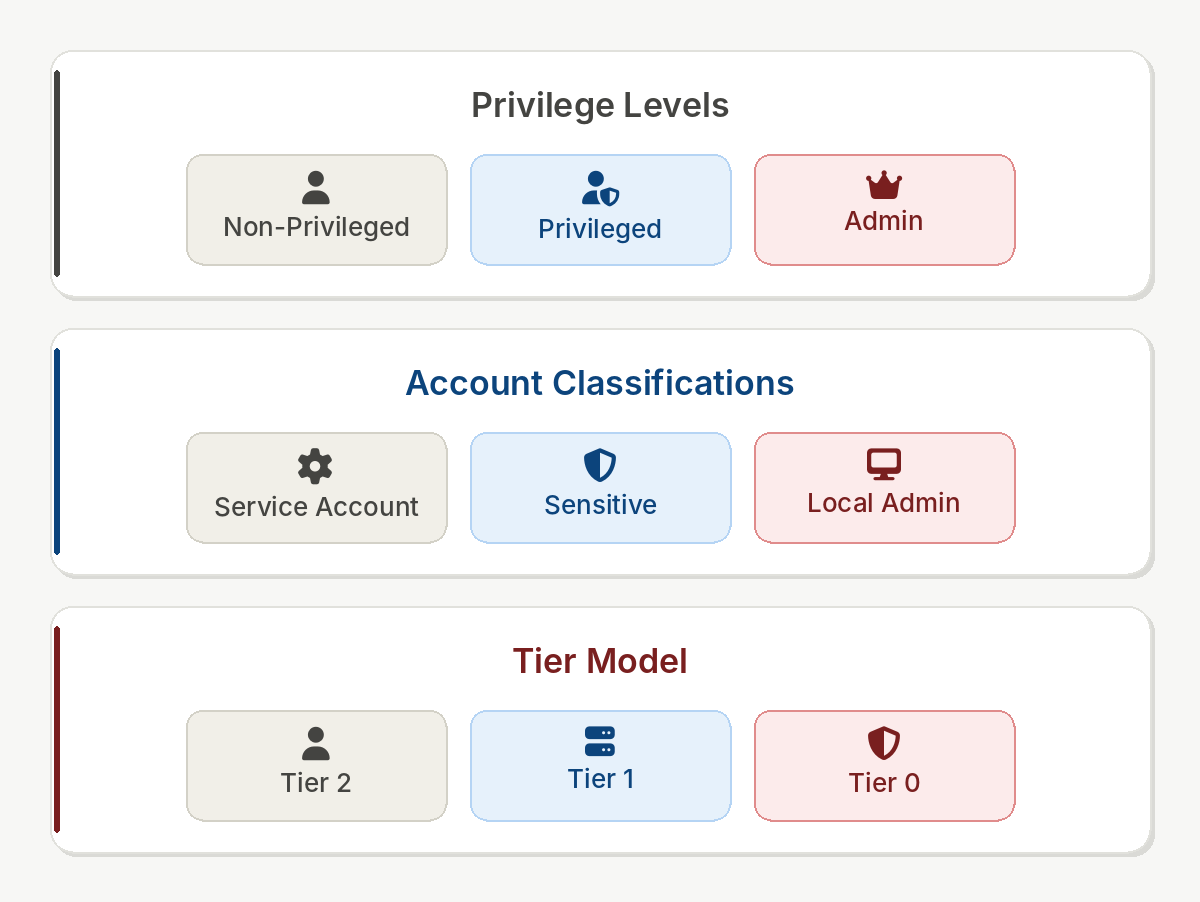
- Generate a complete identity object and privilege inventory within hours
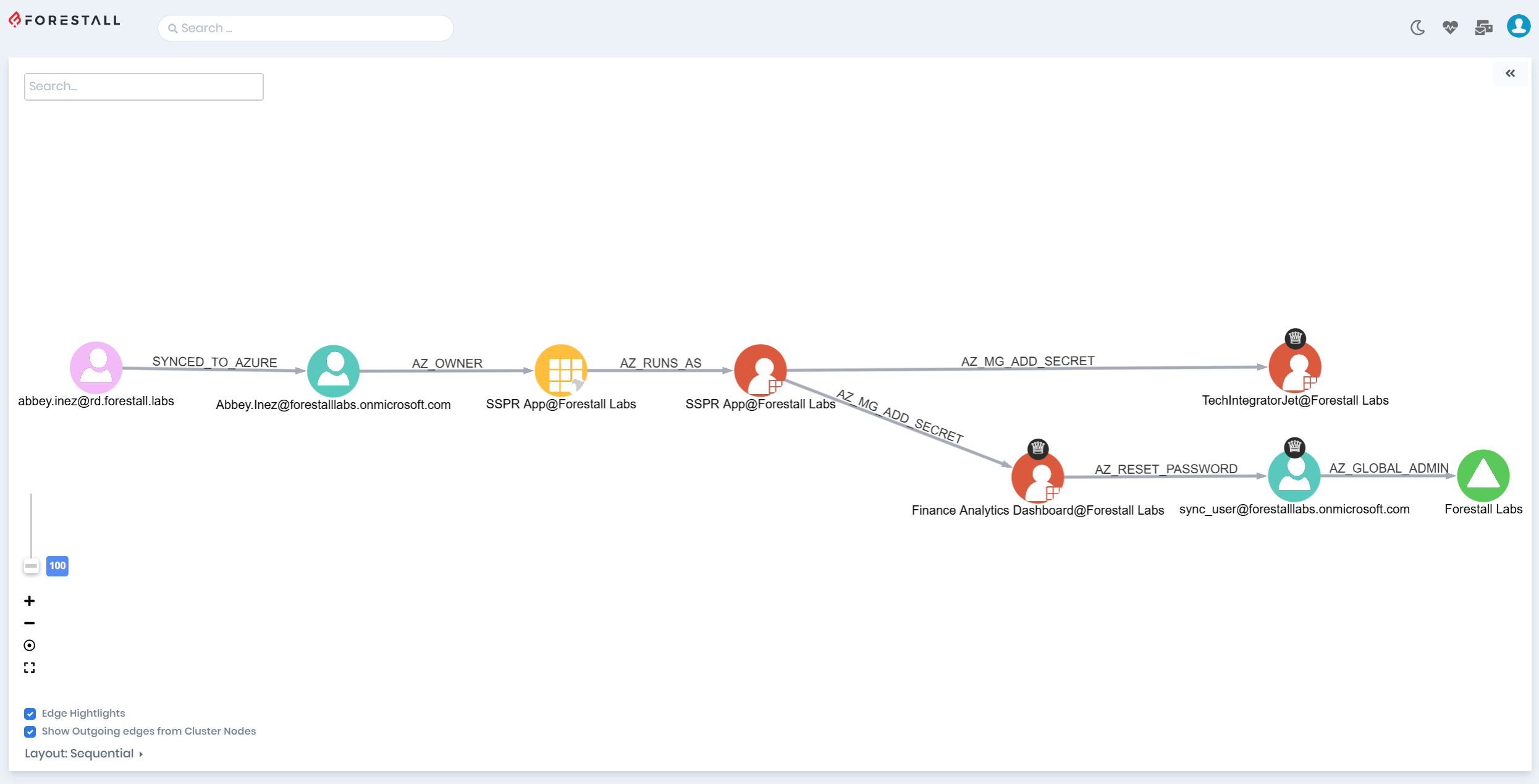
- Identify high-risk trust relationships and excessive privilege assignments
- Produce a posture report documenting identity exposure before integration