Triaging Identity Misconfigurations at Scale
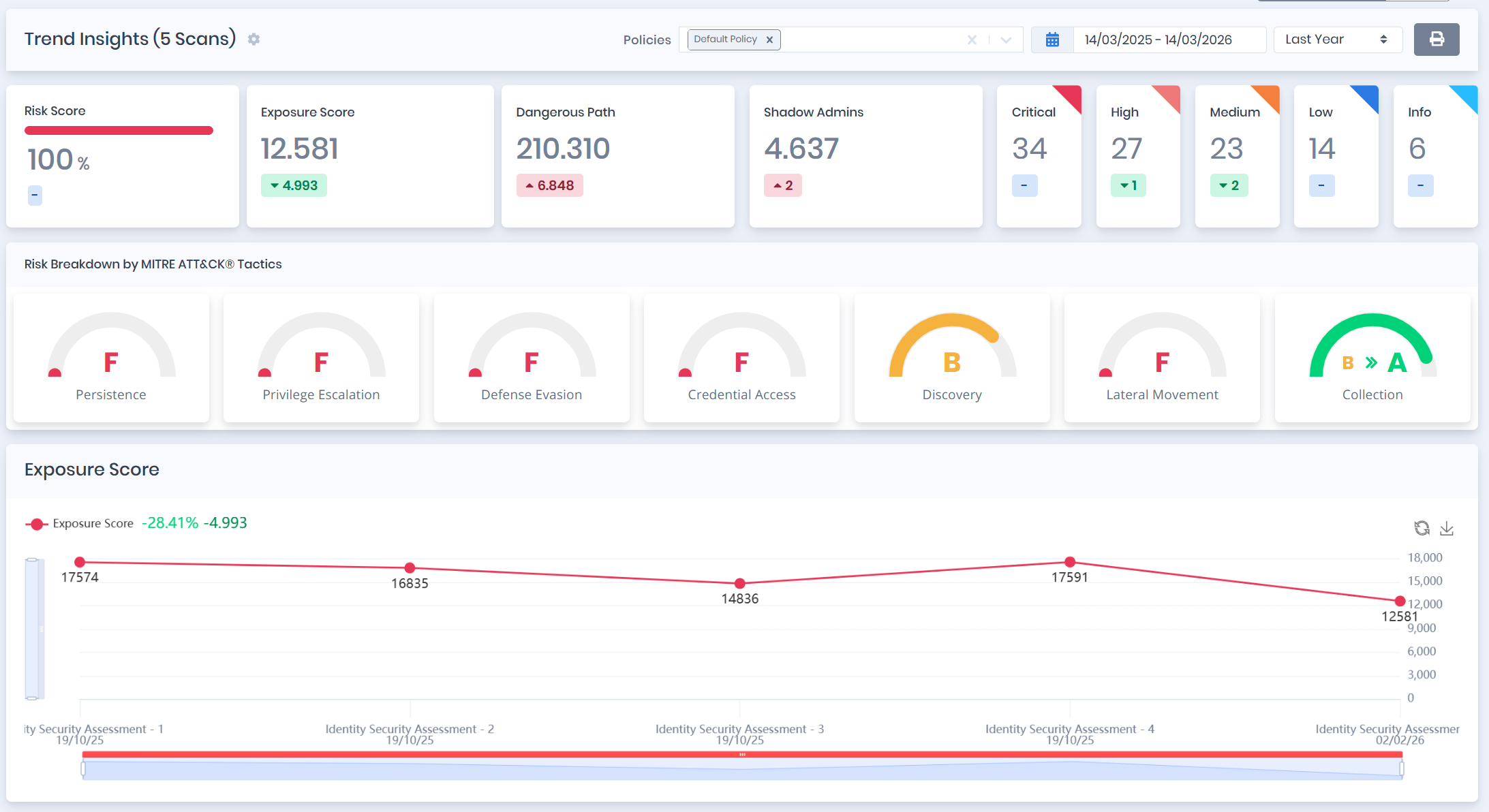
Scenario: A security team inherits an Active Directory environment with thousands of objects and no documentation on which misconfigurations are critical versus cosmetic.
How Forestall helps:
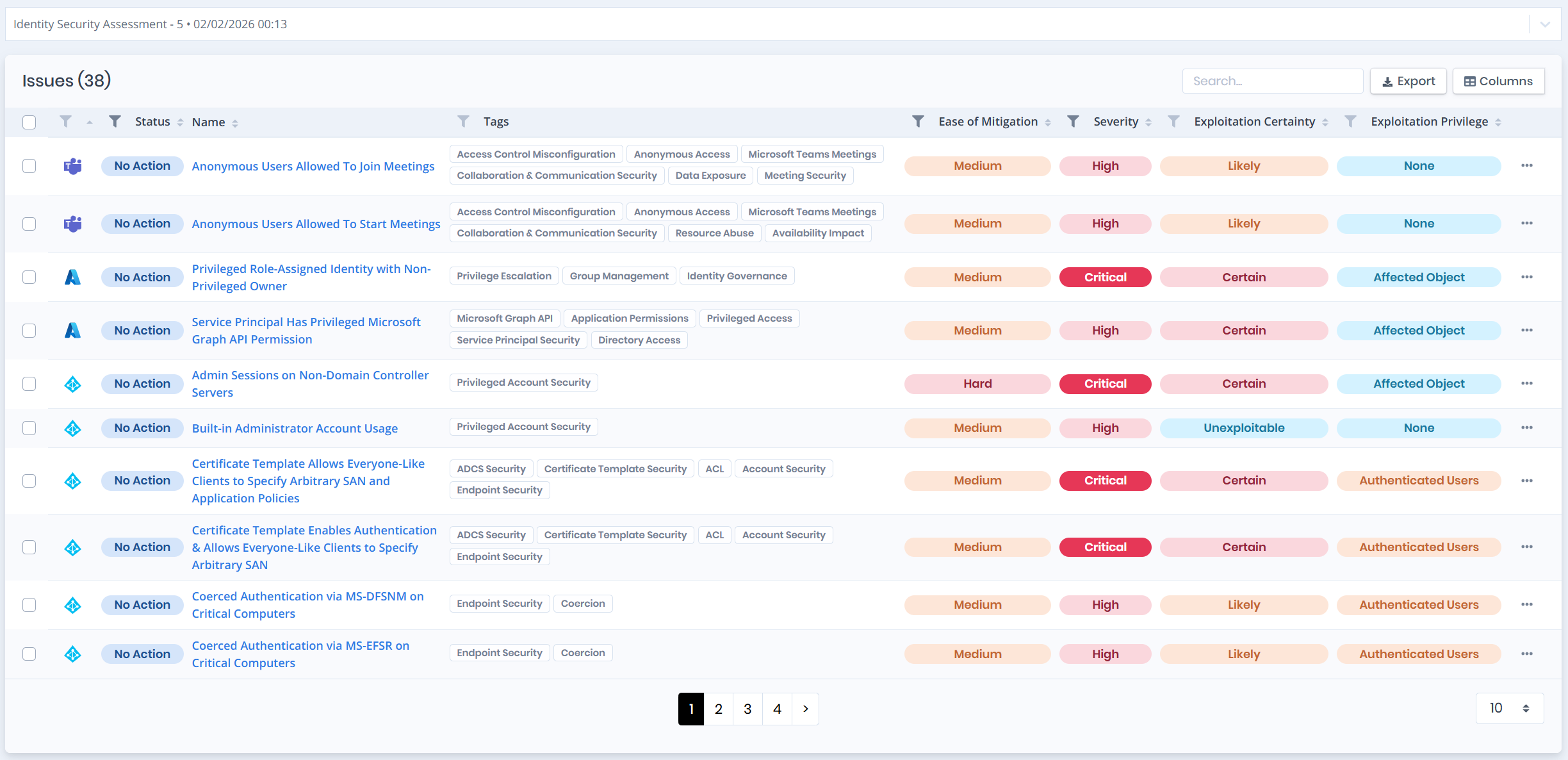
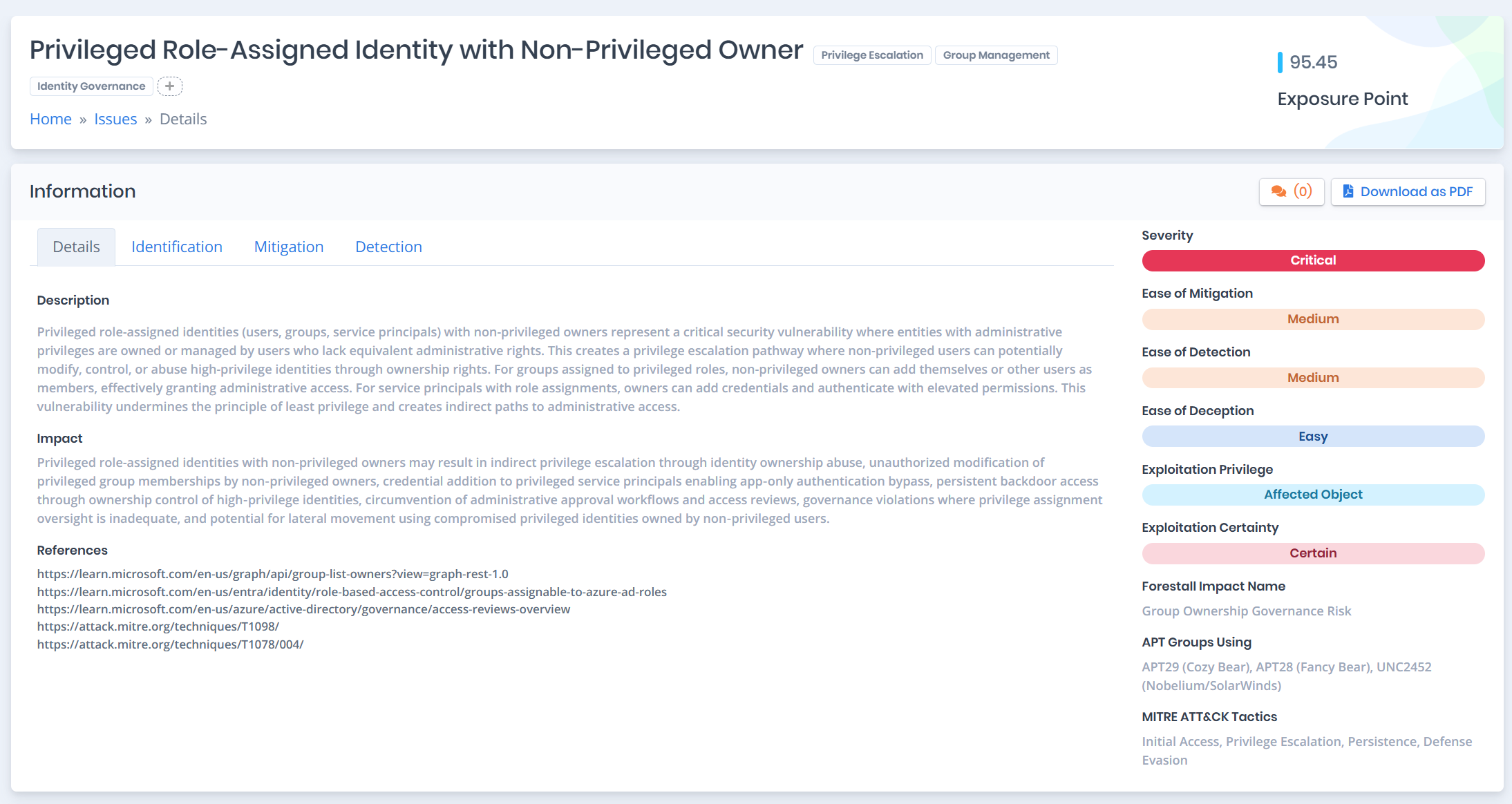
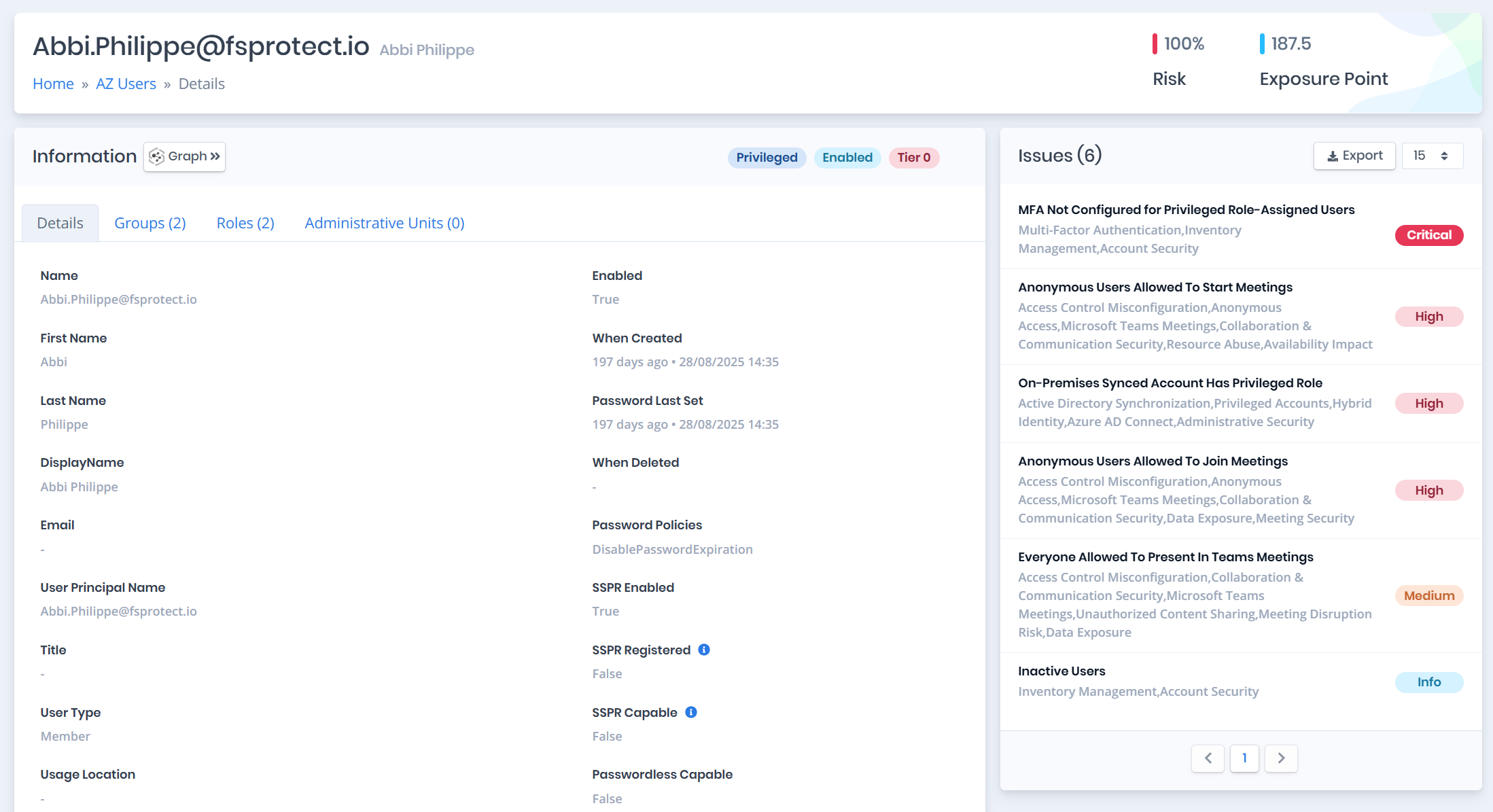
- Detect all misconfigurations across protocols, objects, services, and settings
- Score each finding with exploitation certainty and required privilege metrics
- Generate prioritized remediation queues ordered by impact
- Provide specific remediation guidance for each finding