Post-Breach Credential Assessment
Scenario: After a security incident, the response team needs to determine whether attackers could have accessed credentials stored in file shares from the compromised account.
How Forestall helps:
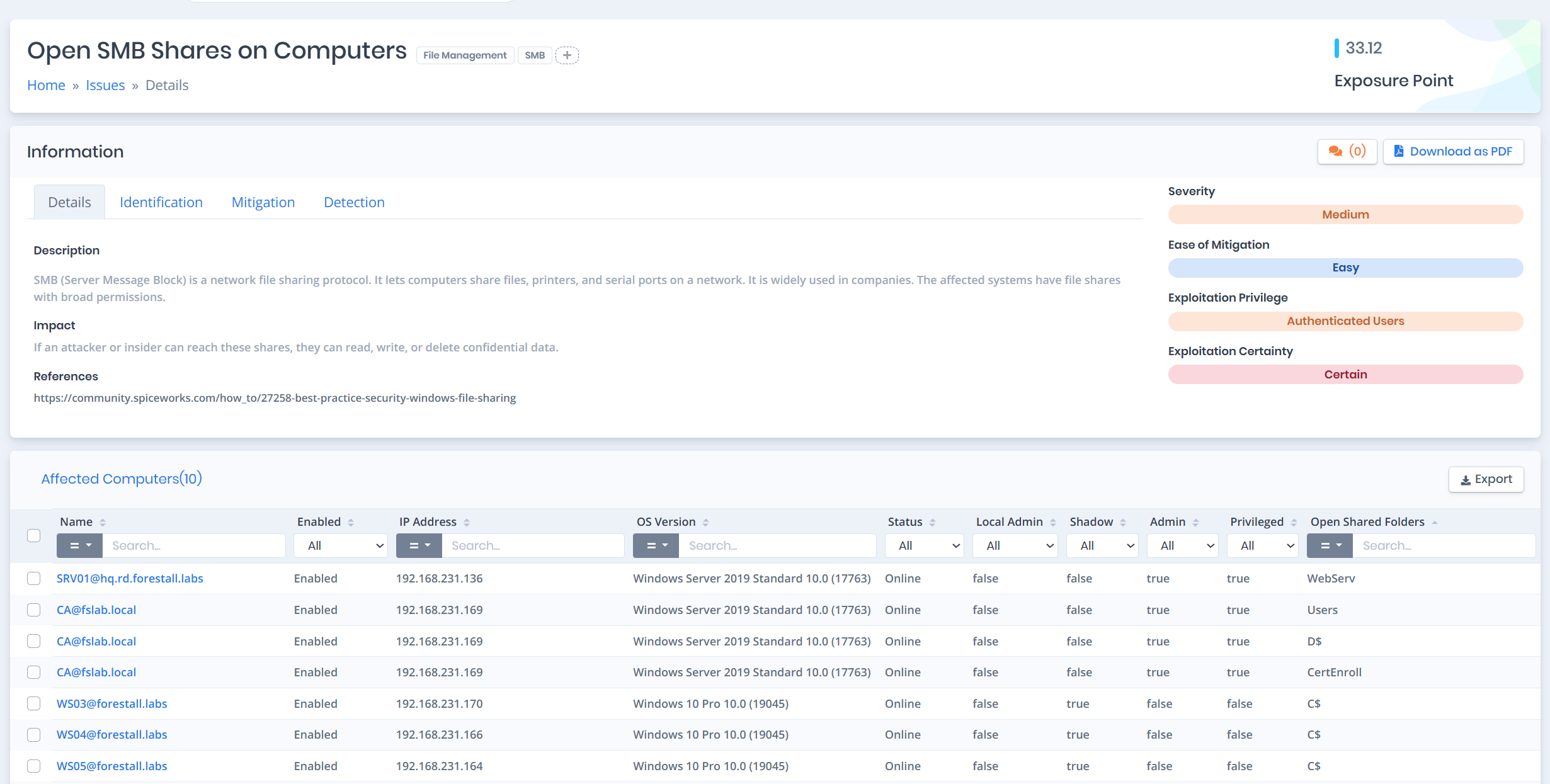
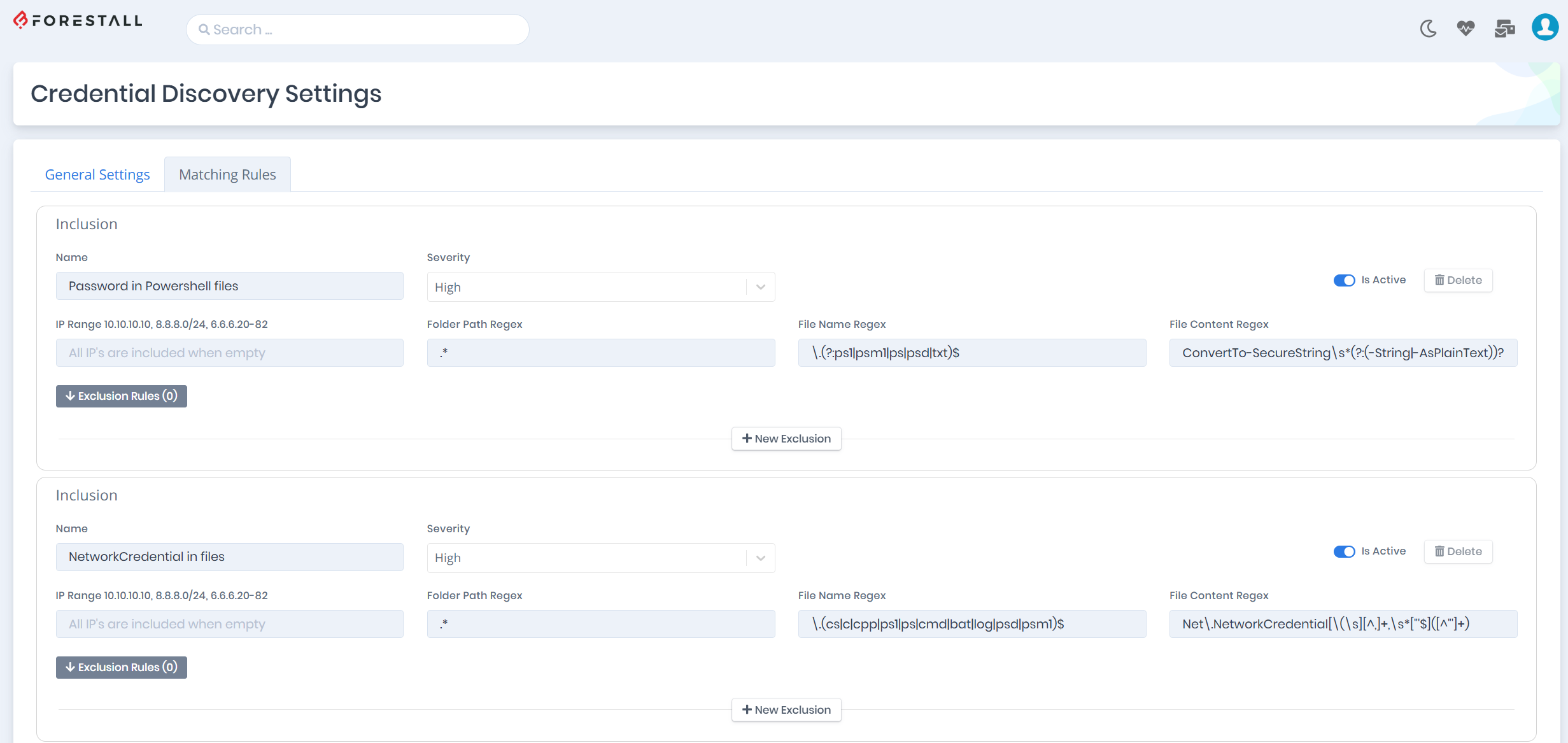
- Scan all accessible file shares from the compromised account context
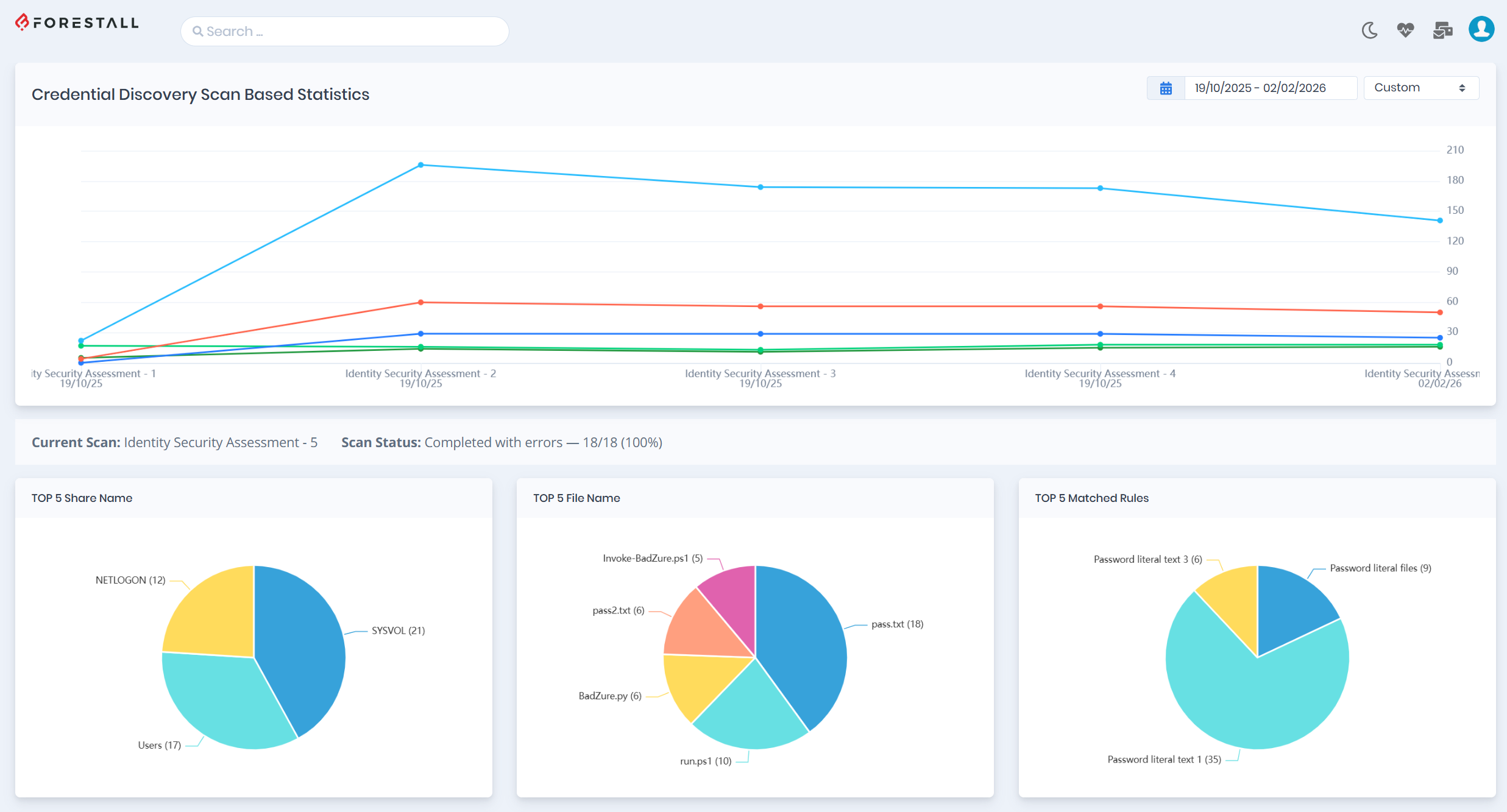
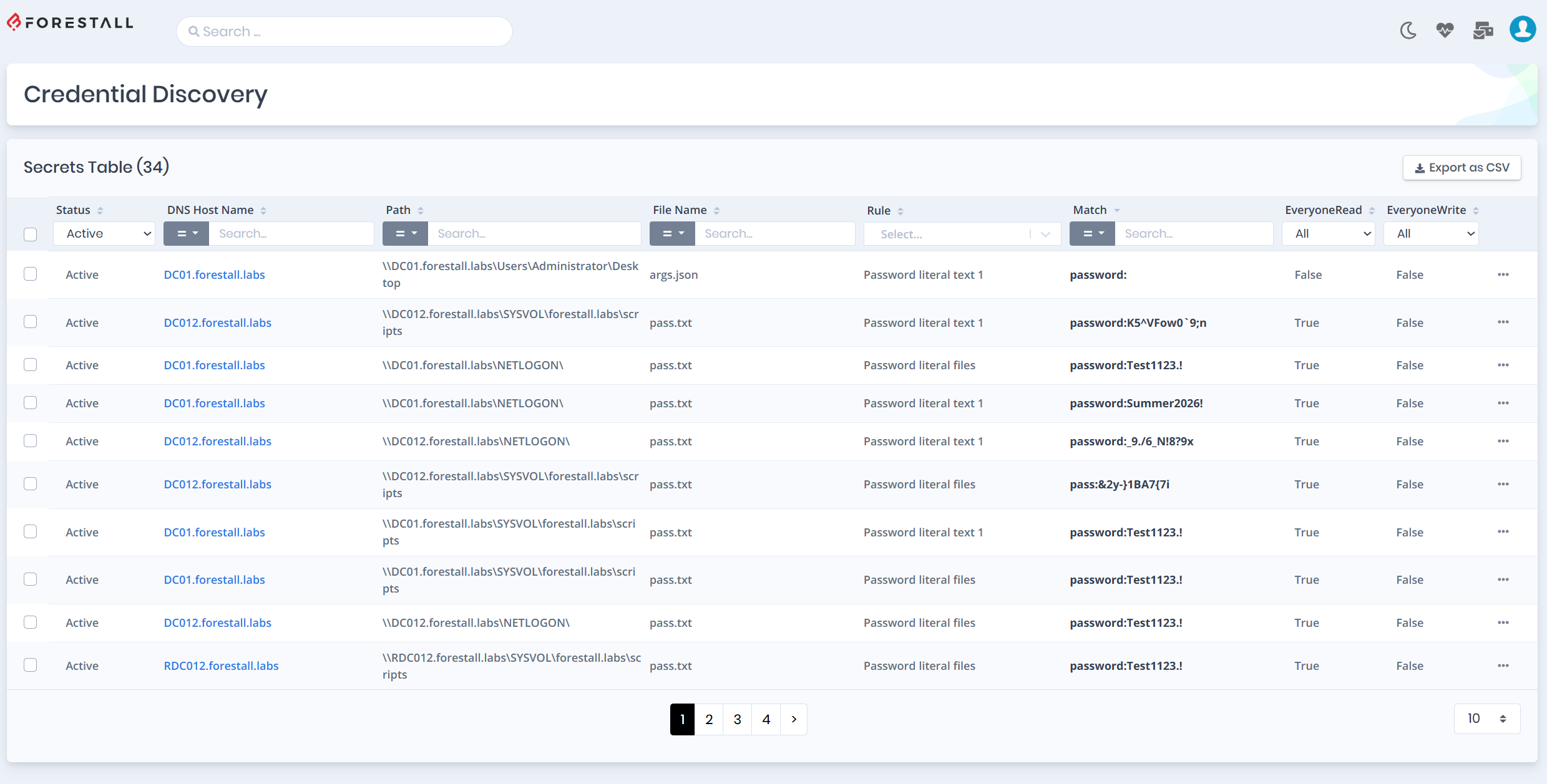
- Identify all exposed credentials the attacker could have reached
- Show the access matrix for each discovered credential
- Prioritize credential rotation based on exposure scope