Detect modern AD vulnerabilities
Scenario: A red team operator needs to quickly identify exploitable weaknesses across AD protocols before an engagement deadline.
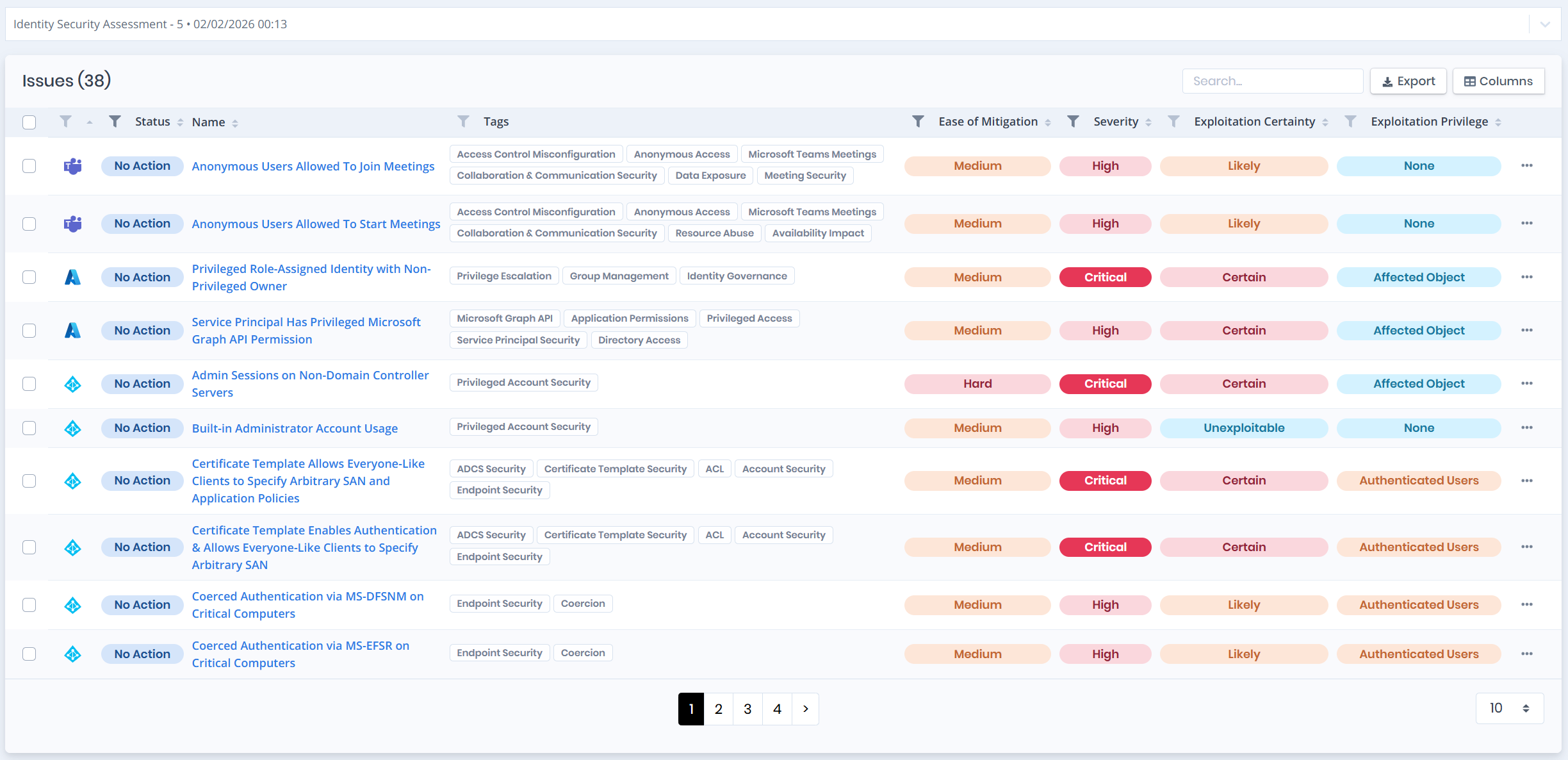
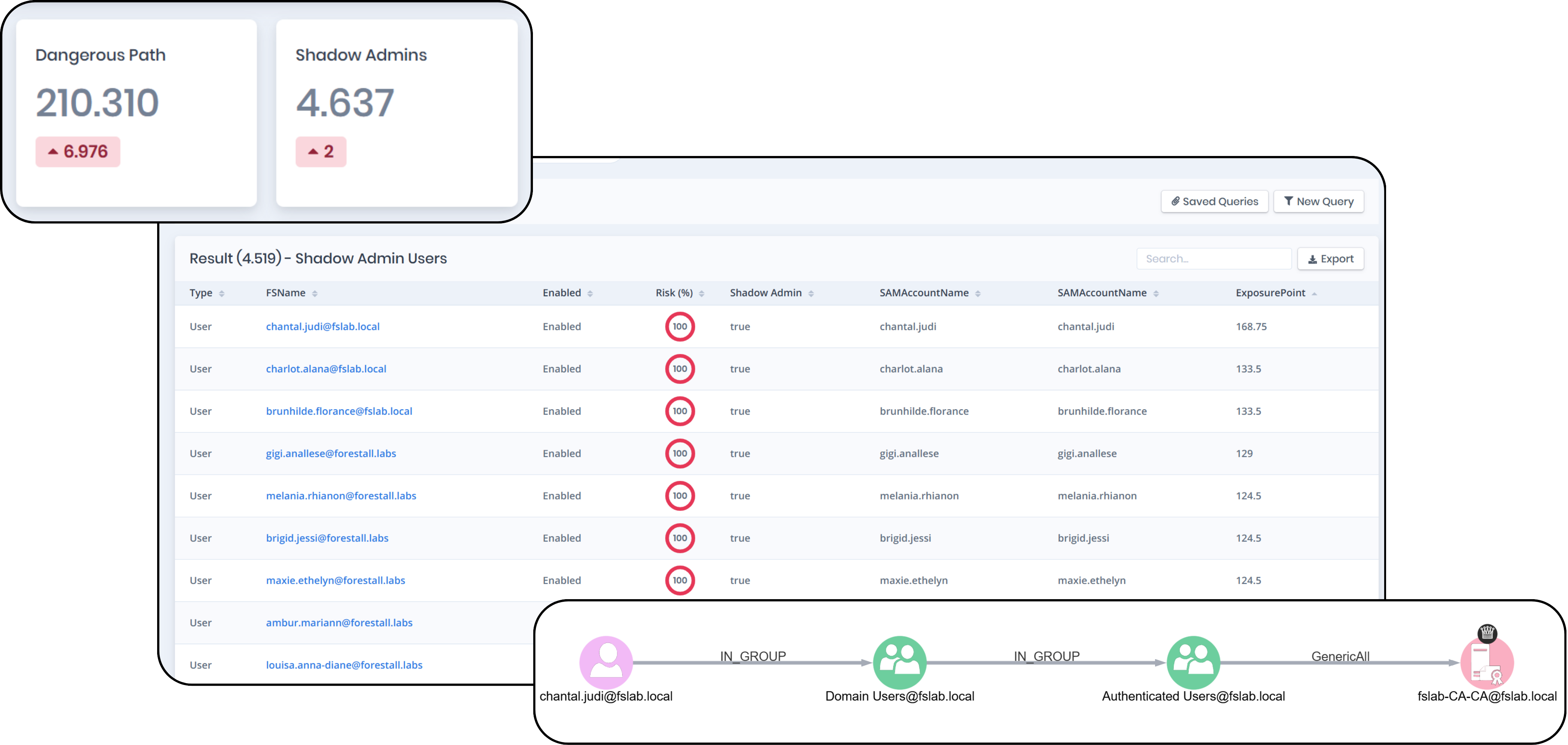
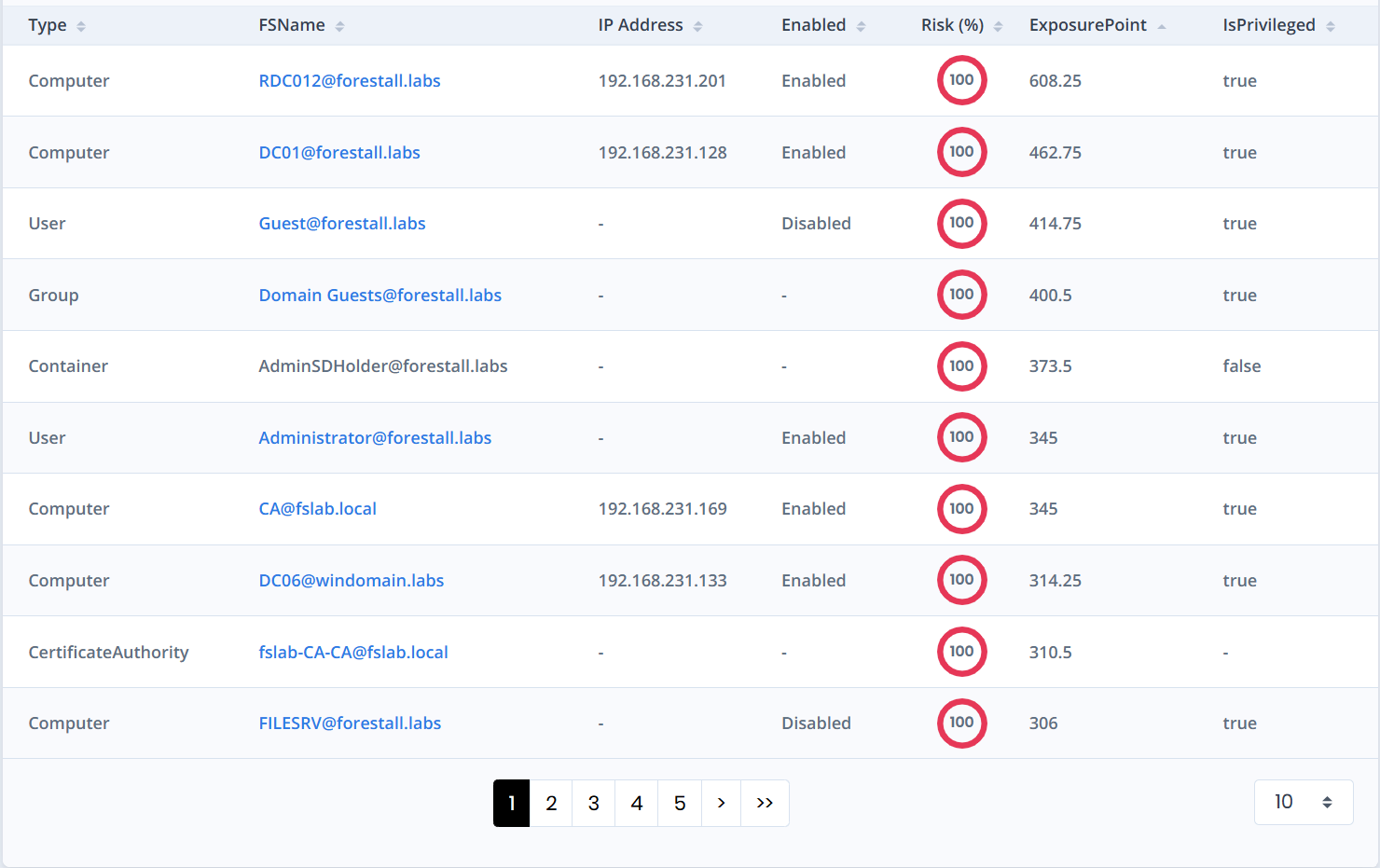
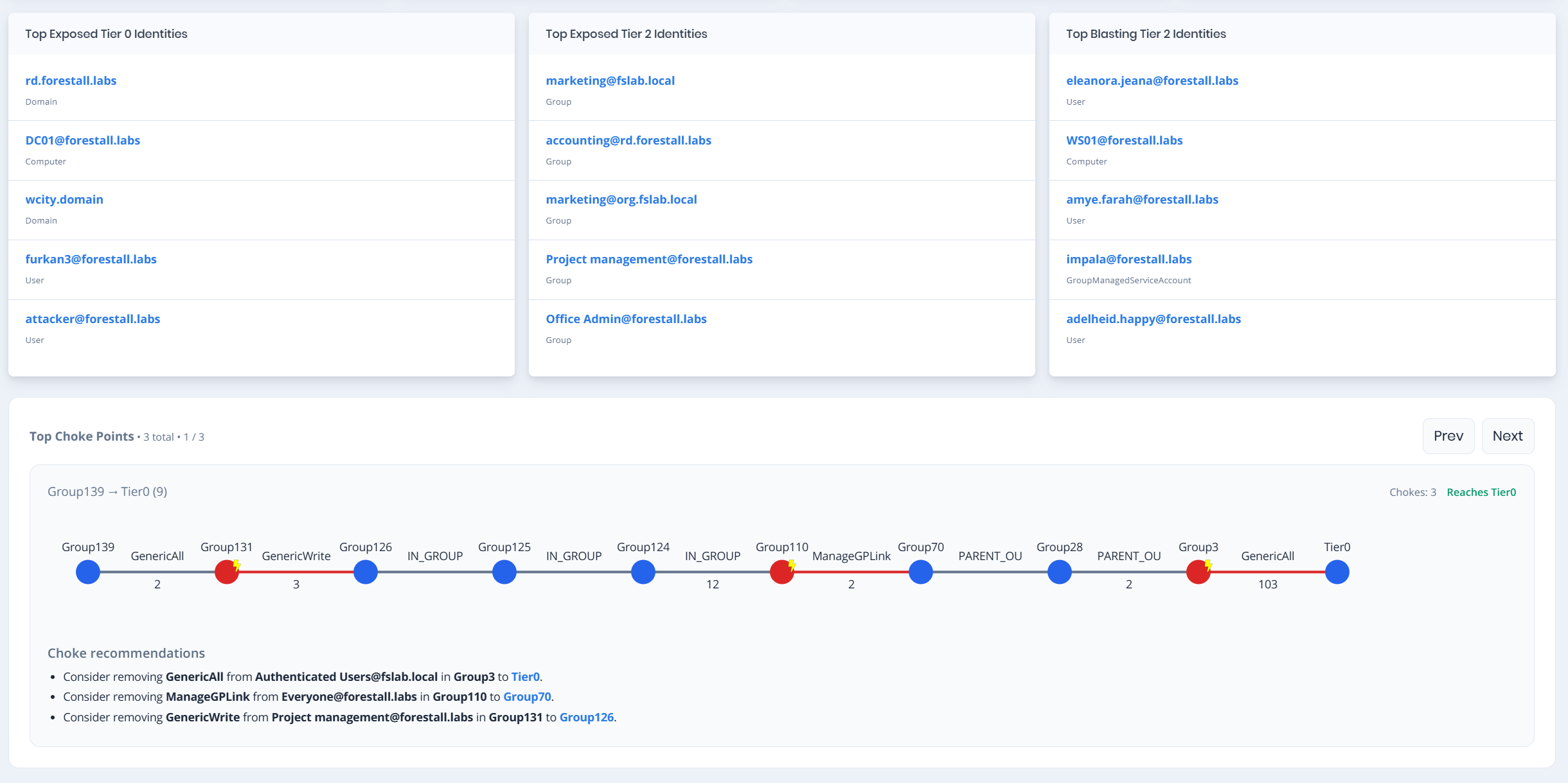
Problem: Critical AD security gaps hide across identity protocols and services.
What Forestall does:
- Finds security gaps across identity protocols and services (Kerberos, NTLM, SMB, LDAP, RPC)
- Highlights high-impact weaknesses including certificate services and trust misconfigurations