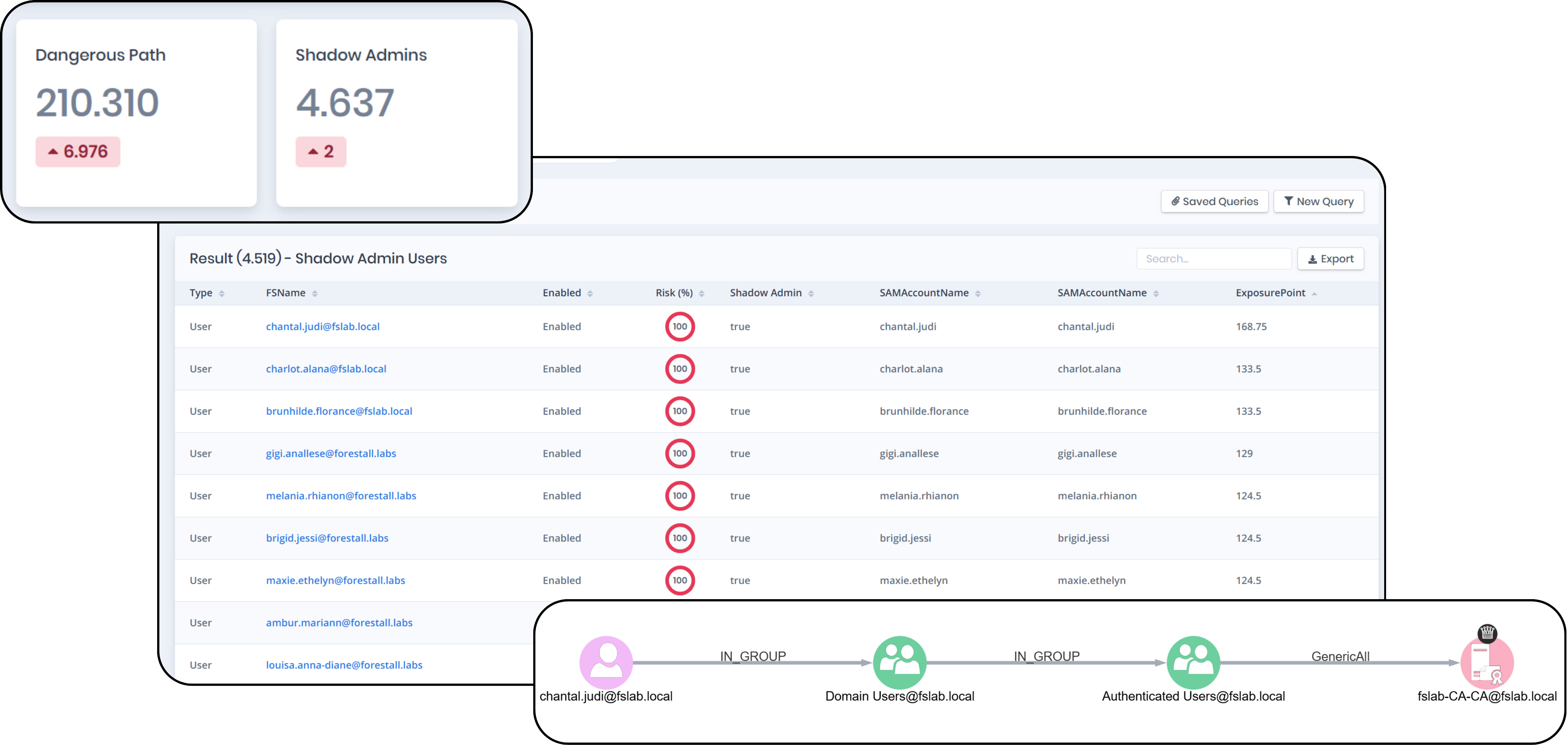
Rapid escalation to Tier 0 after initial access
Scenario: An attacker phishes a help desk user and within minutes finds a privilege escalation chain leading to Domain Admin.
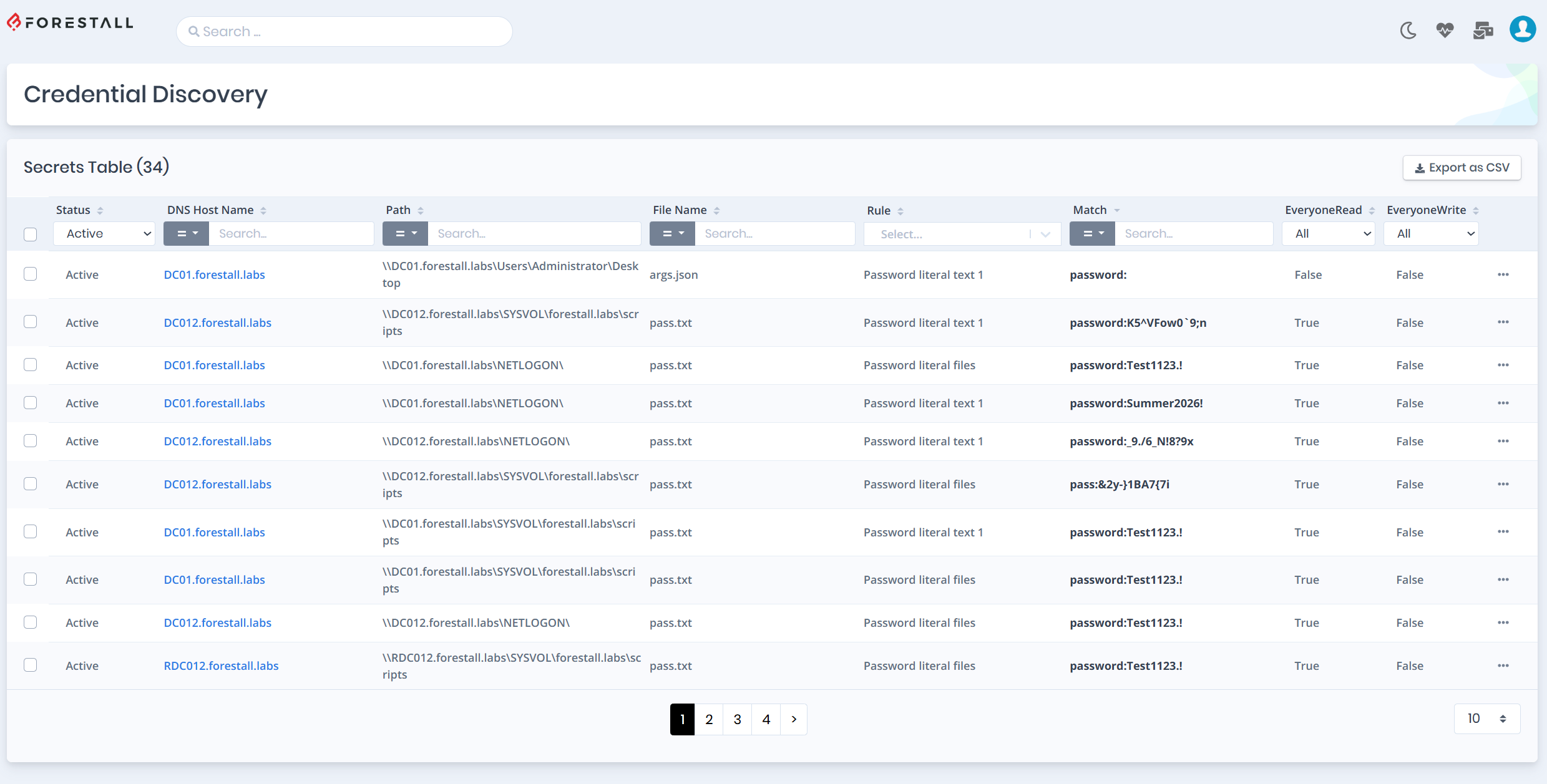
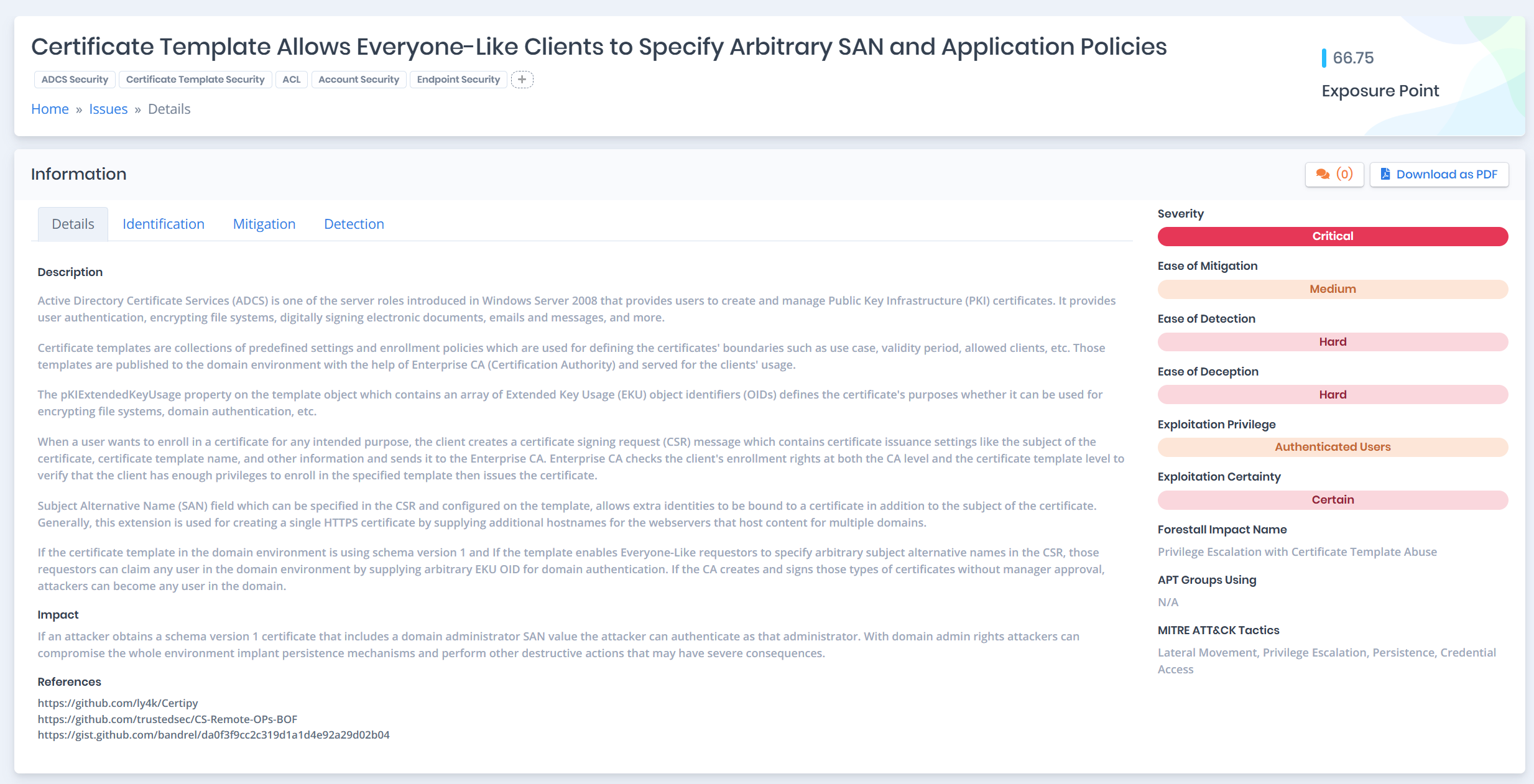
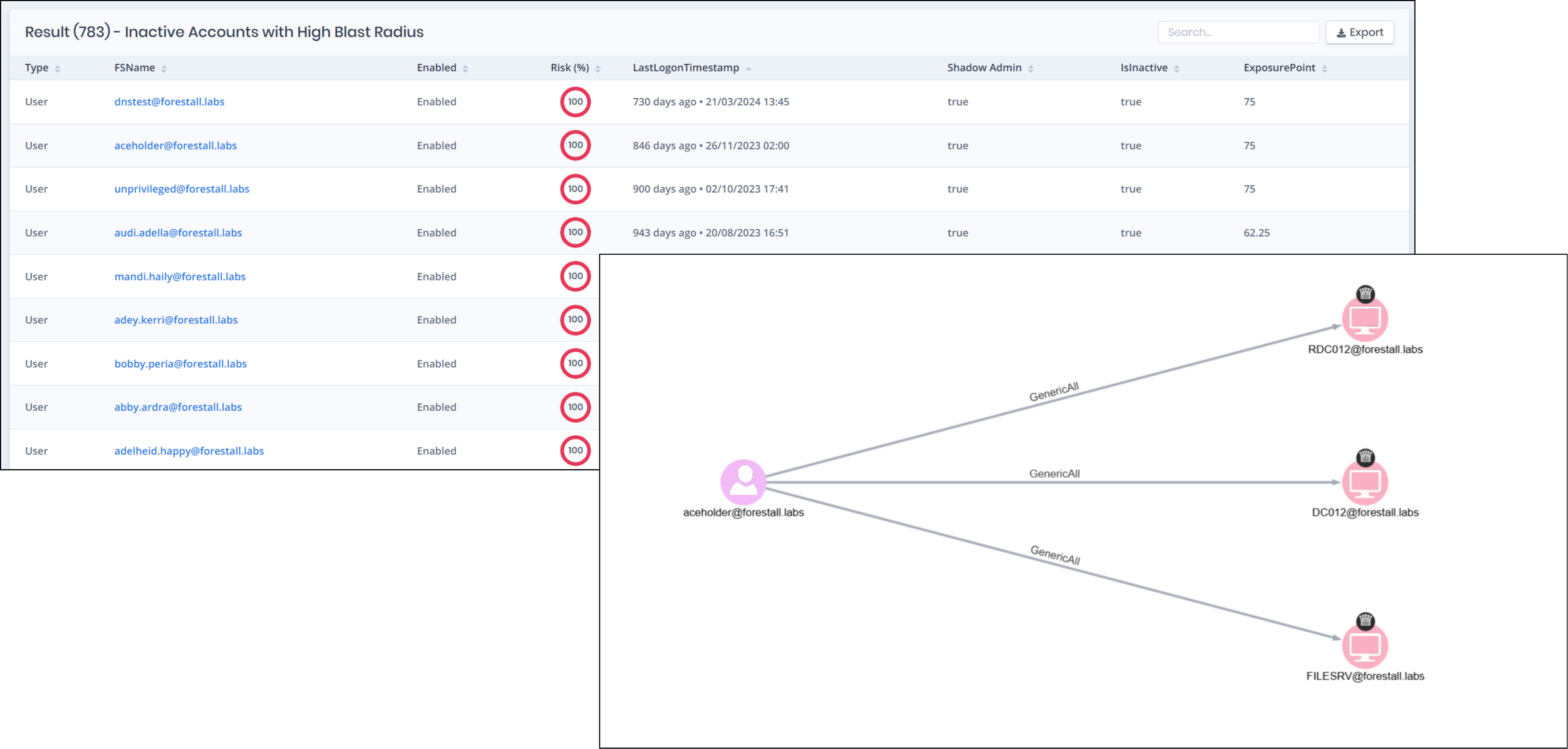
Problem: Attackers escalate quickly to Tier 0 through hidden privilege paths after initial compromise.
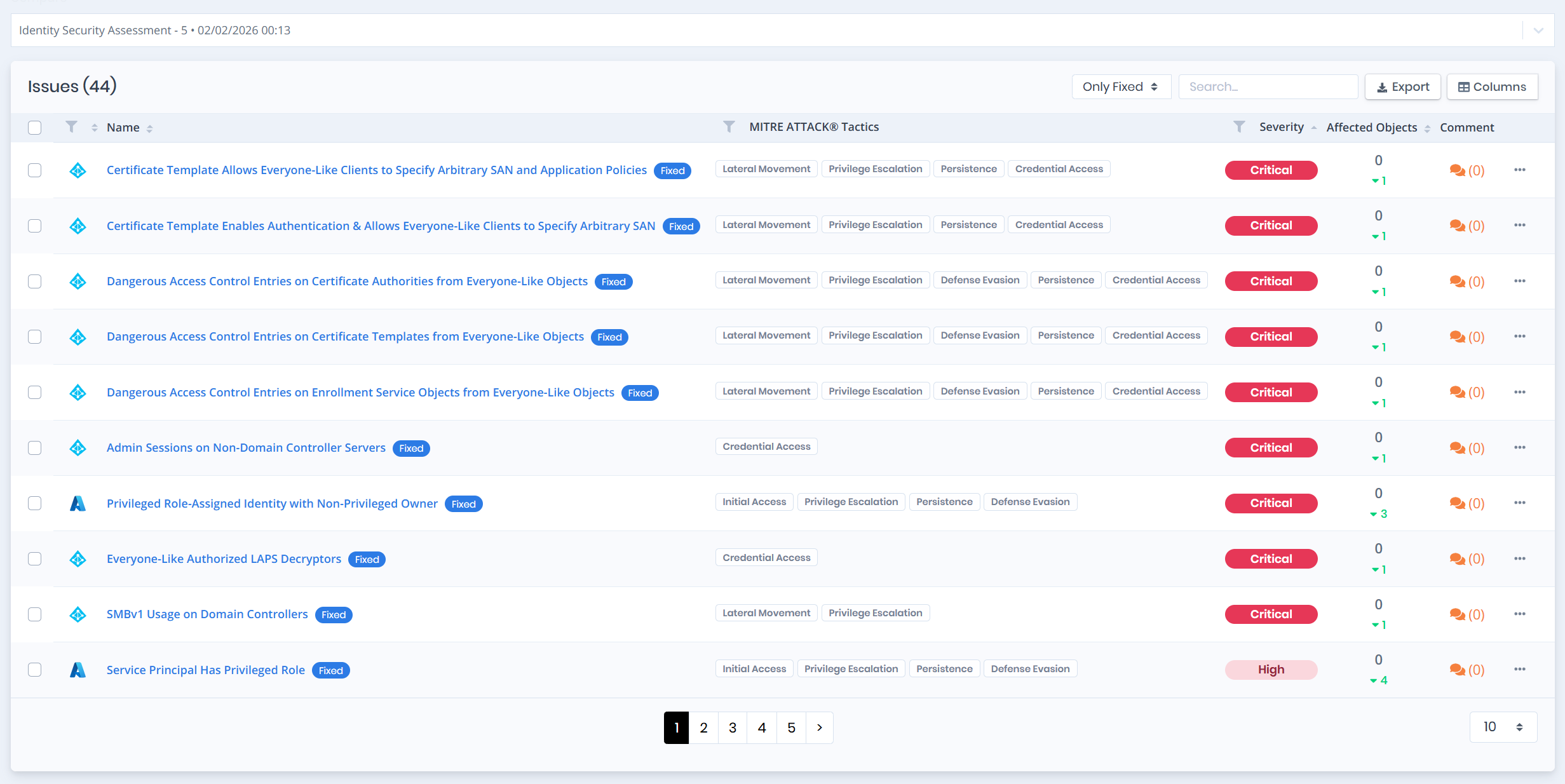
What Forestall does:
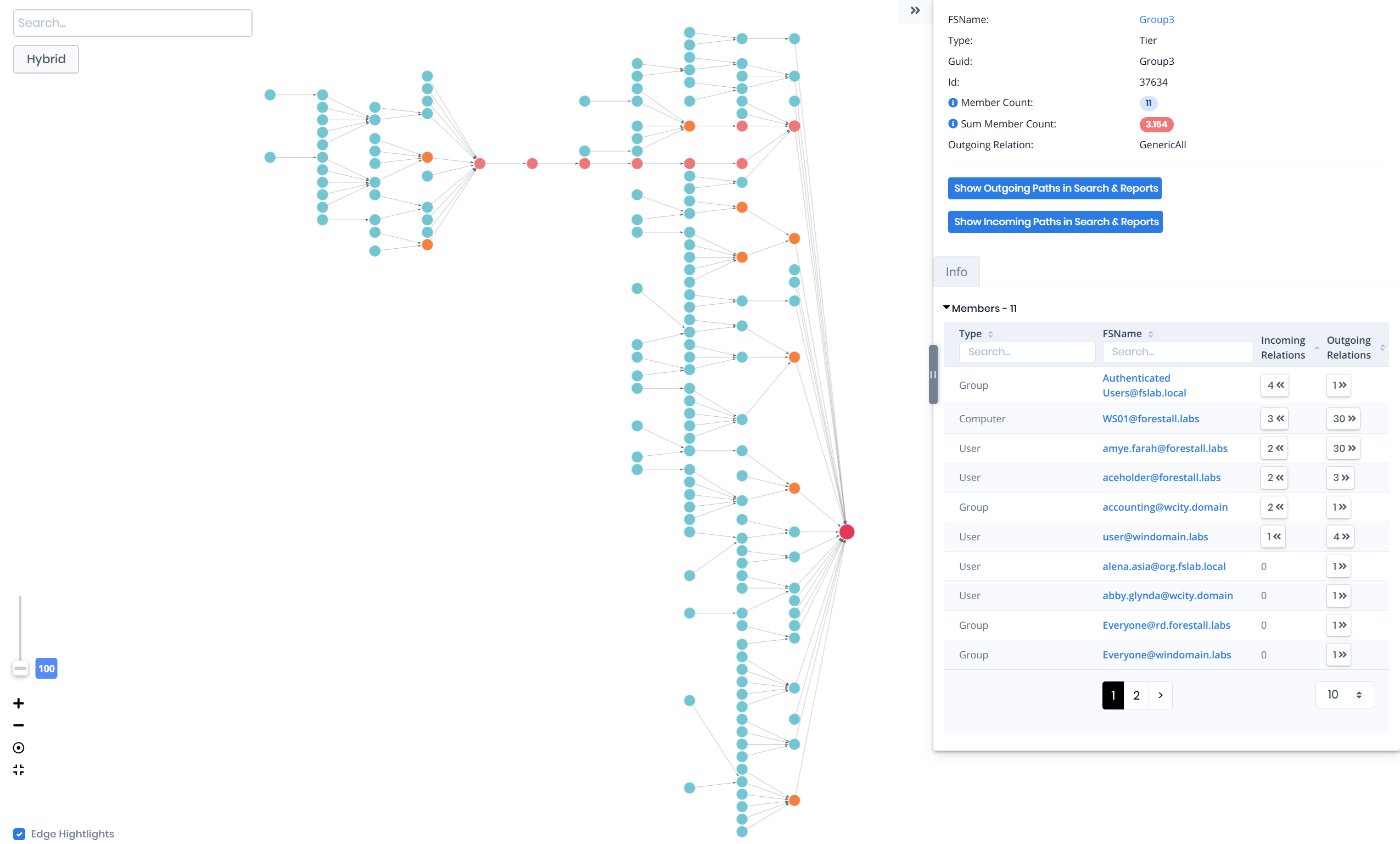
- Finds shortest privilege escalation paths to Tier 0 and crown-jewel identities
- Highlights path drivers (delegation, ACLs, misconfigs, trust edges)