Privilege creep detection
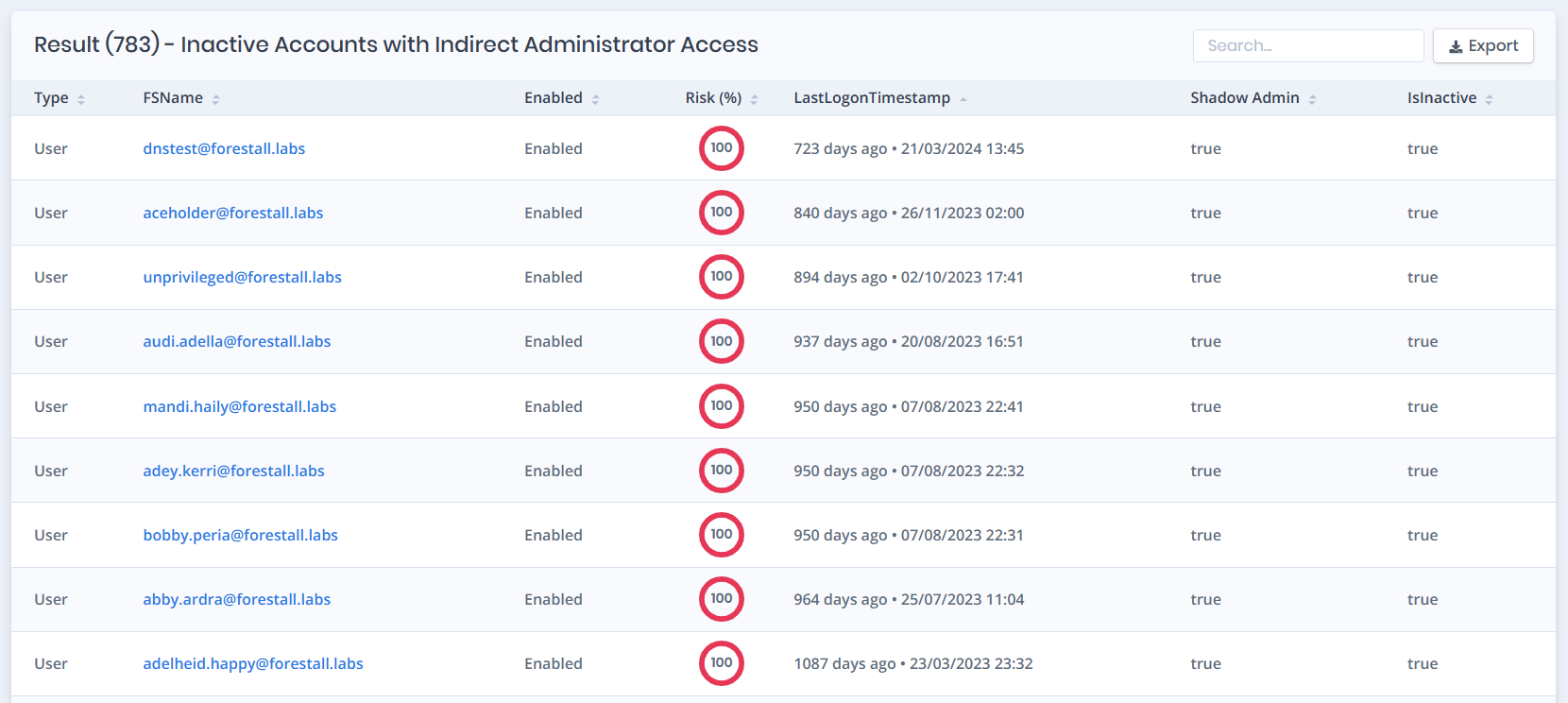
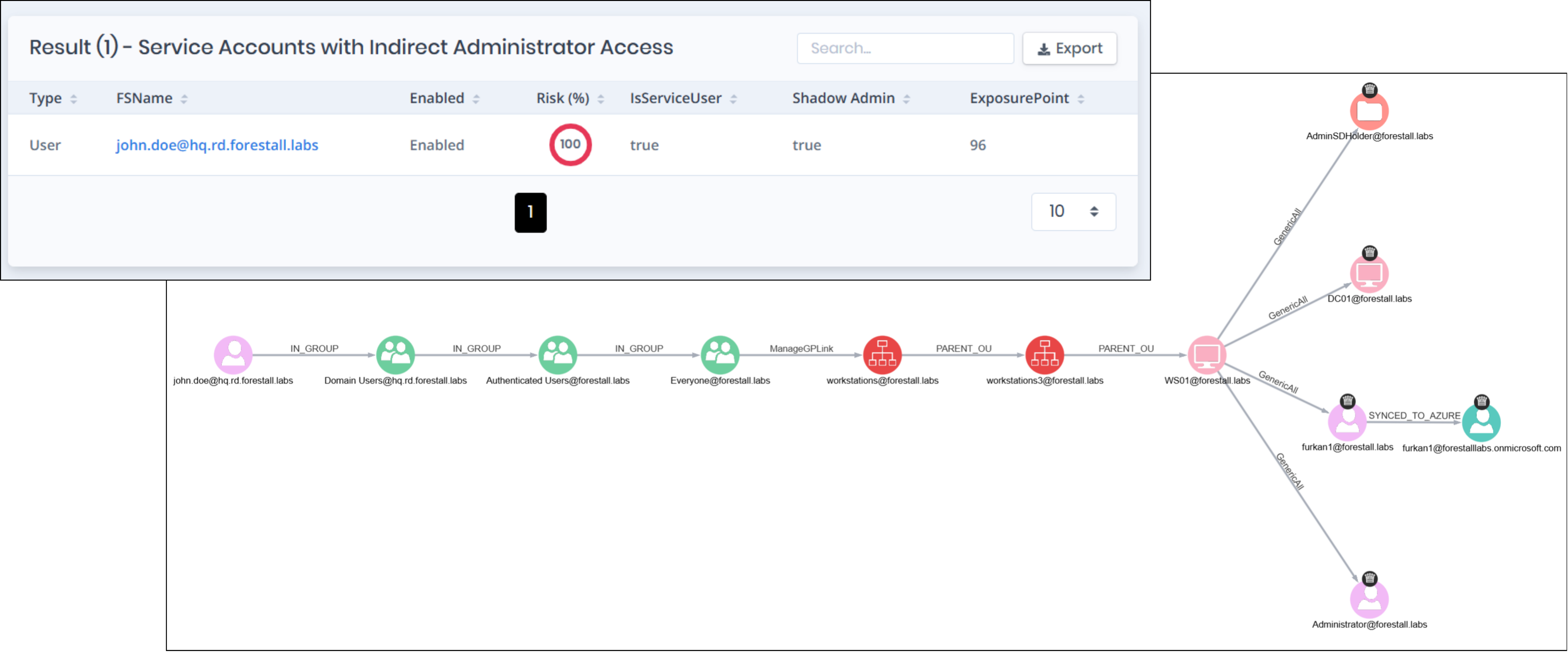
Scenario: A user who changed roles two years ago still holds admin-equivalent access through nested group memberships nobody reviewed.
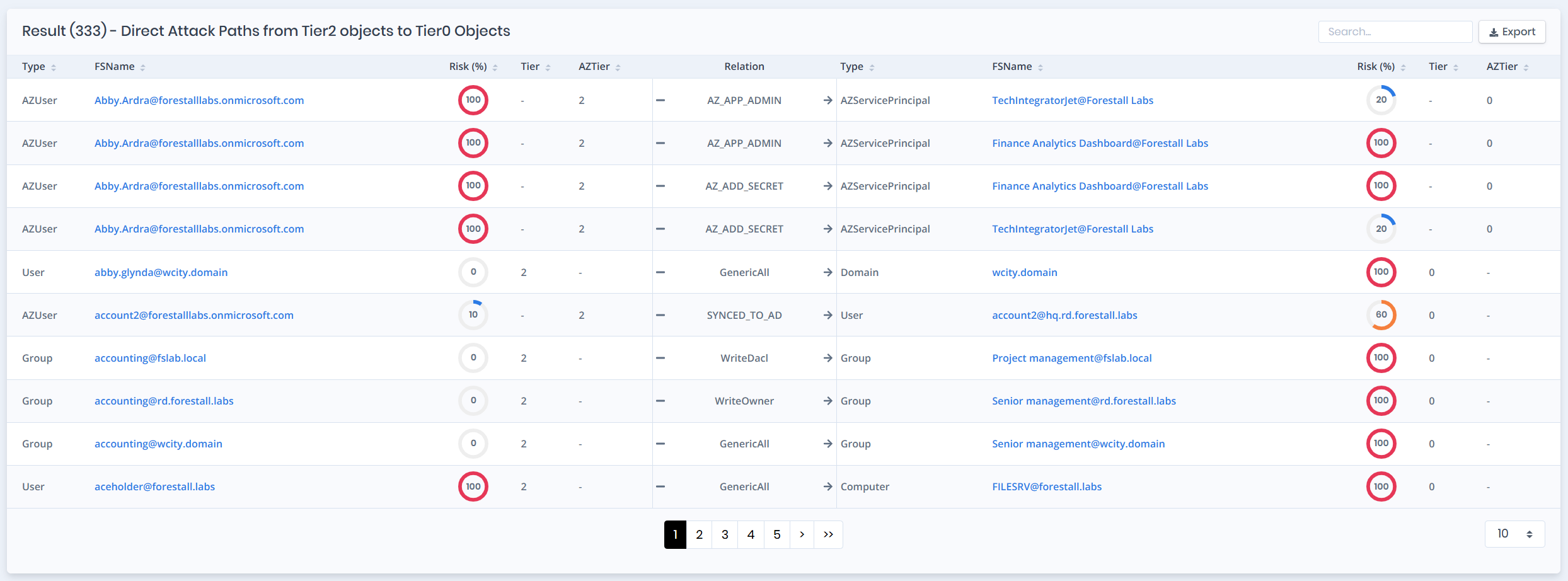
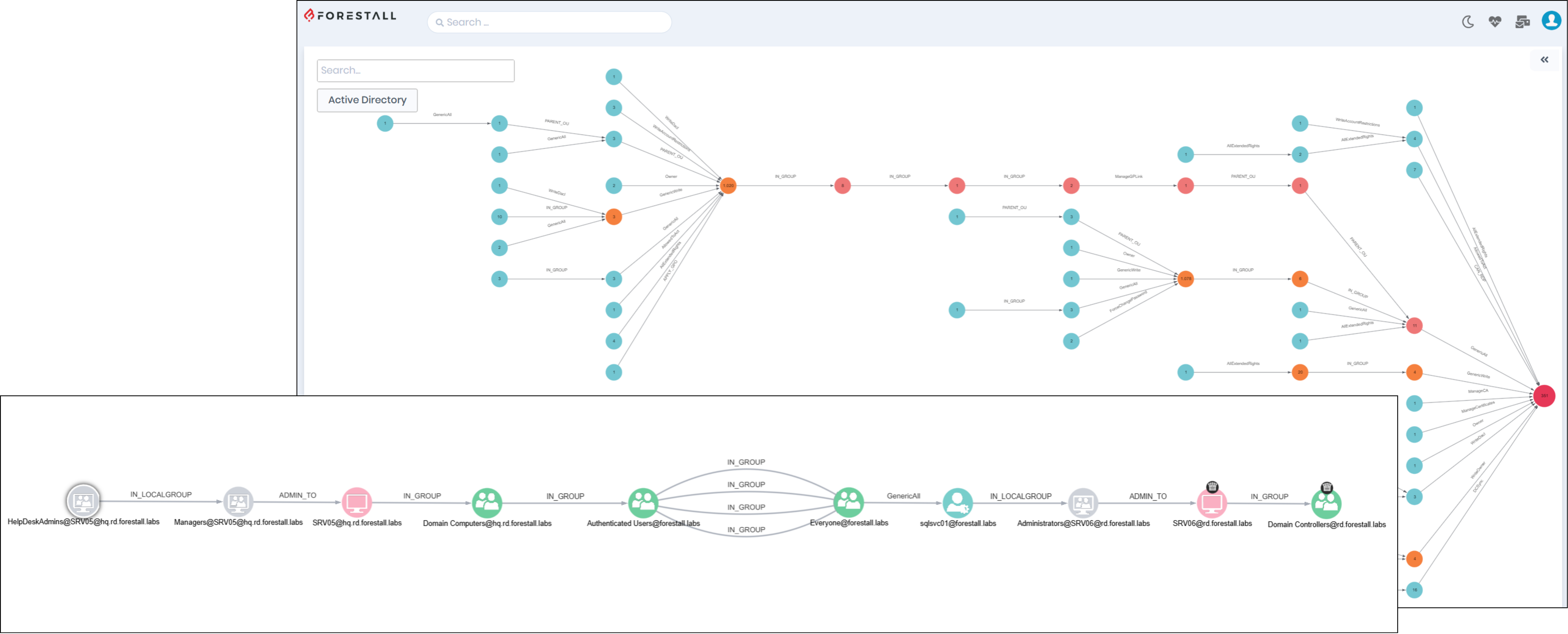
Problem: Indirect privilege through nesting, delegation, and ACL inheritance goes undetected.
What Forestall does:
- Finds indirect privilege through nesting, delegation, and ACL inheritance
- Highlights cleanup actions with lowest operational risk