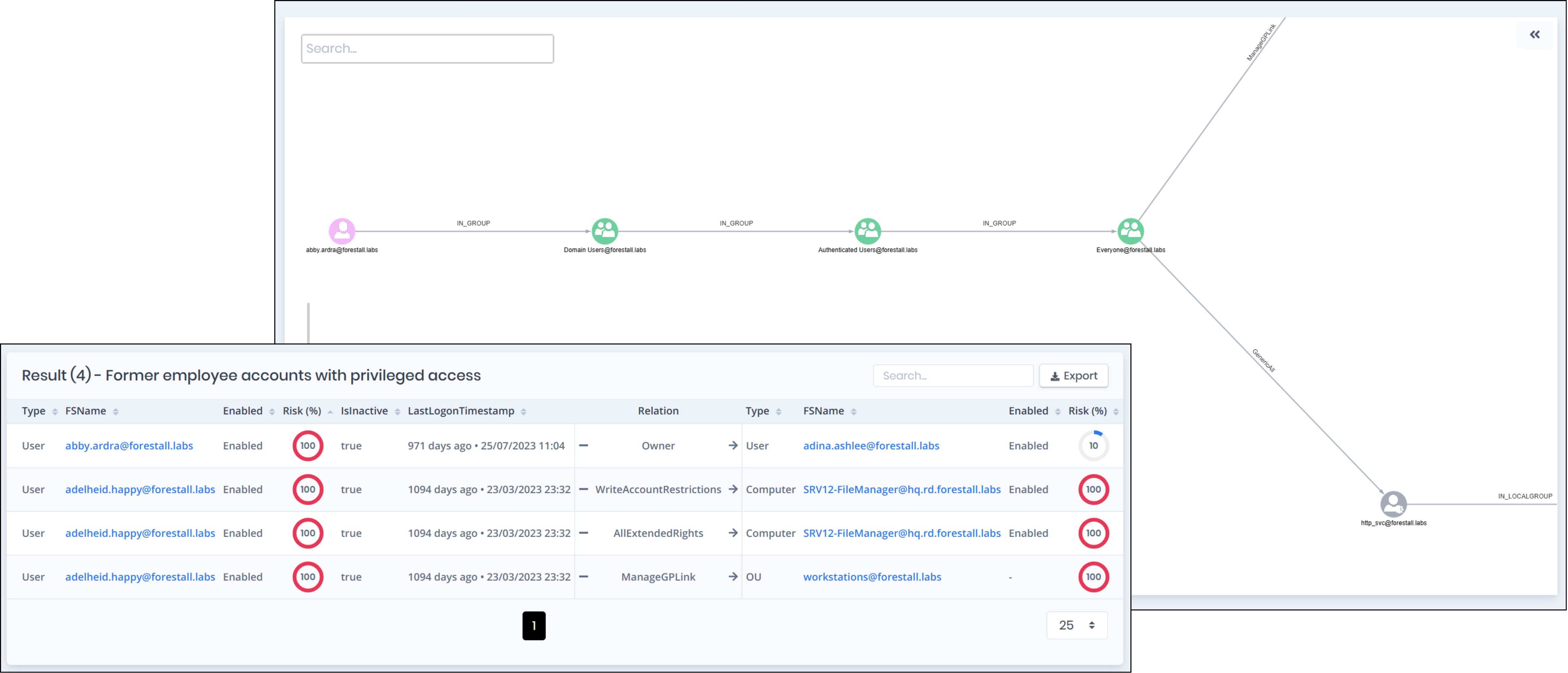
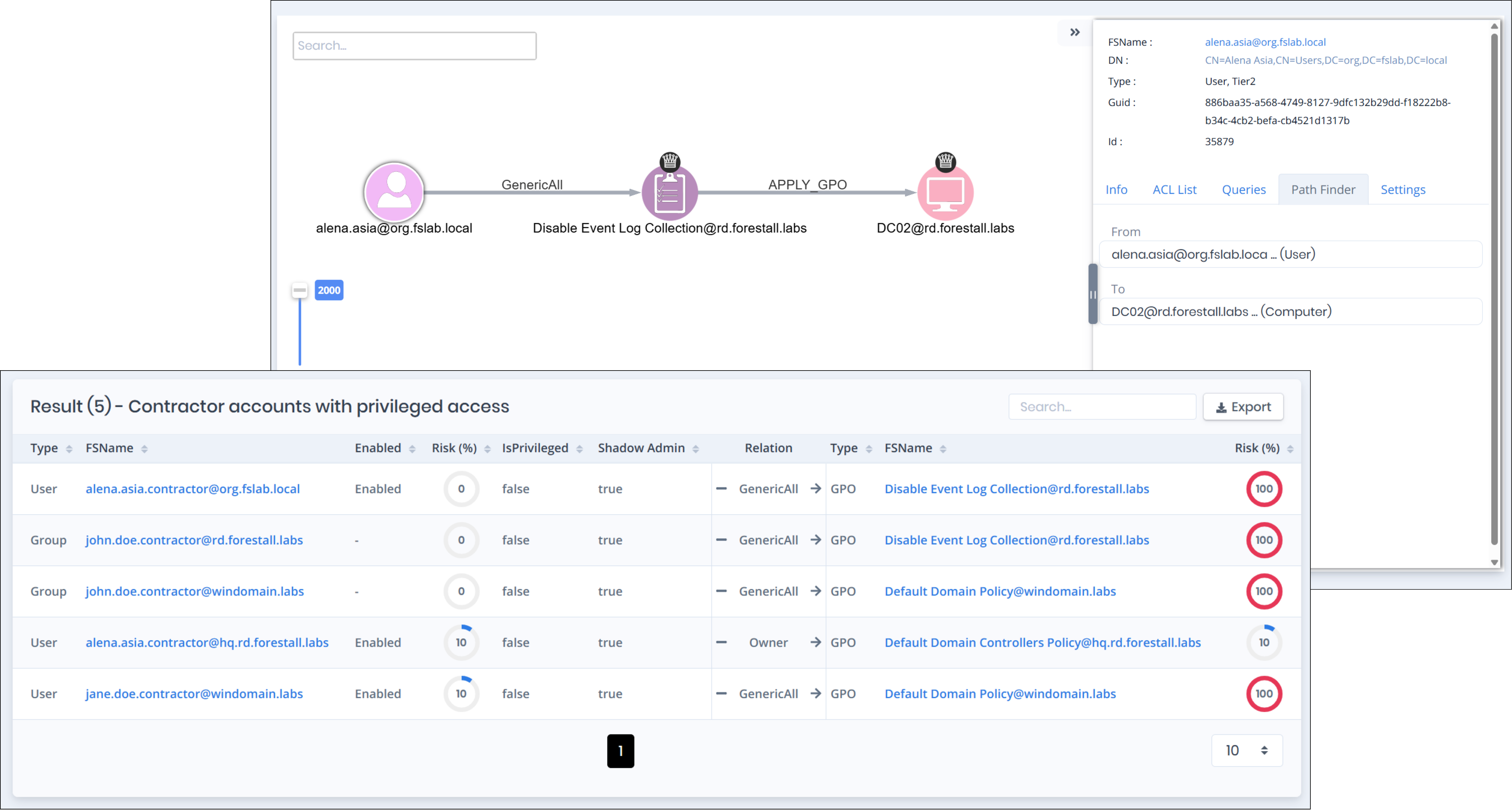
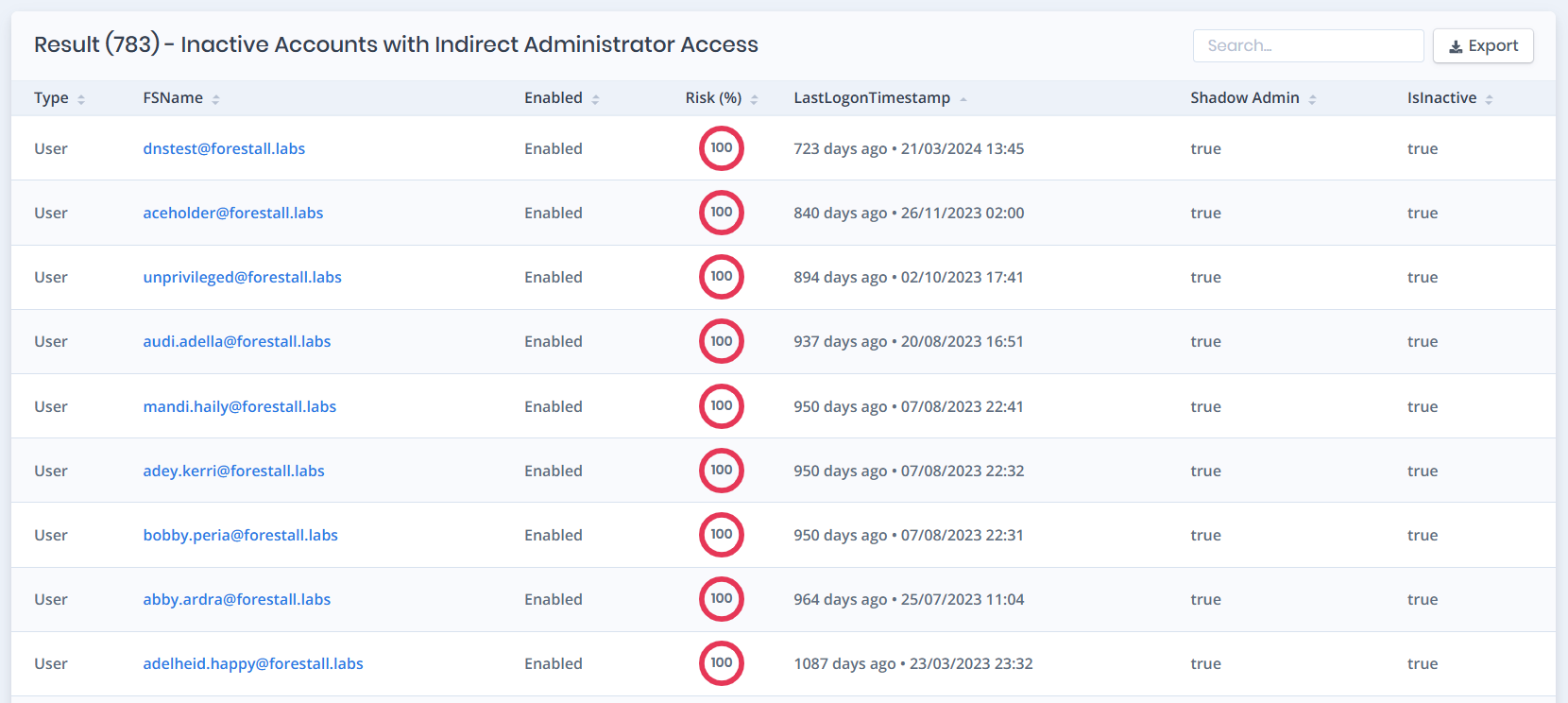
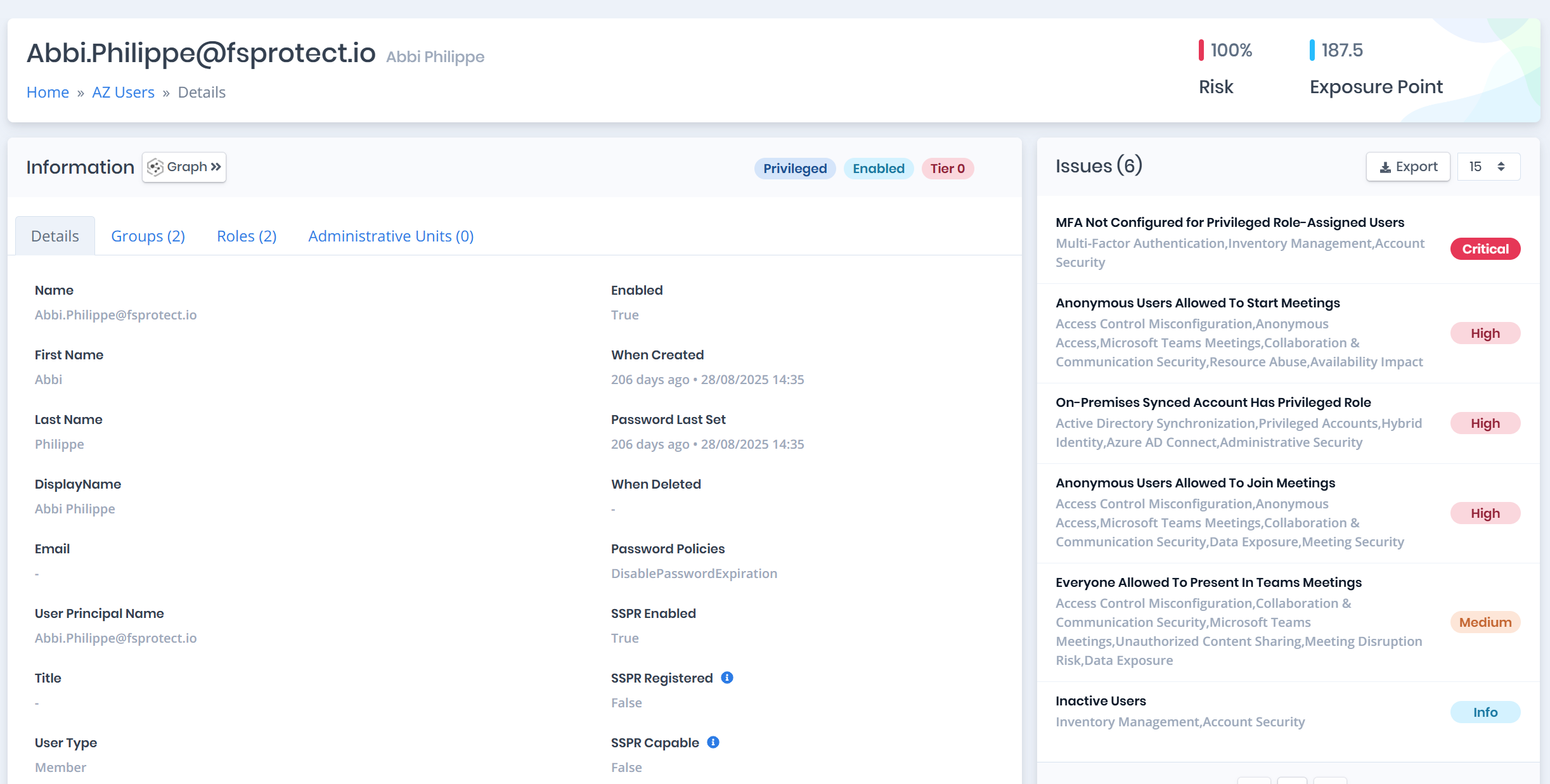
Privilege creep through nesting and inherited access
Scenario: A departing employee still has admin-equivalent access through three levels of nested group membership that was never cleaned up.
Problem: Indirect privilege through groups, ACL inheritance, and delegation goes undetected in reviews.
What Forestall does:
- Finds indirect privilege grants via groups, ACL inheritance, and delegation
- Highlights the smallest changes that reduce the most risk